Scenario 9 - Remote Access VPN Dashboard
Objectives
- What - A remote access VPN serves as a secure portal for users to connect to corporate networks from any location. Ideal for remote or traveling employees, as it provides a seamless link to the organization's internal resources. The sensor is our Firewall Threat Defense (FTD) device.*
- Why - Filter, search, and export data. Historical reporting of VPN sessions, and usage patterns.
- How - Verify connectivity to inside network, and explore the RAVPN dashboard.
Secure Firewall acts as a sentinel, deploying features like intrusion prevention, malware defense, and URL filtering to fortify communication channels against evolving cyber threats. The integration of remote access VPN with Secure Firewall doesn't just secure the gateway; it fortifies the entire organizational posture. It's a meticulous blend of secure connectivity and advanced threat protection, creating a resilient defense against the challenges posed by cyber threats in the digital landscape.
Lab Tasks
These are the tasks in the scenario below. If you are familiar with the Secure Firewall you may do these on your own, or for step-by-step instructions see below.
- Task 1 - Verify the connectivity to inside network.
- Task 2 - Explore the RAVPN Dashboard.
Warning
Completion of the PBR with SGT/User Identity lab is imperative before attempting this exercise. Failure to do so may result in unsuccessful outcomes for this lab.
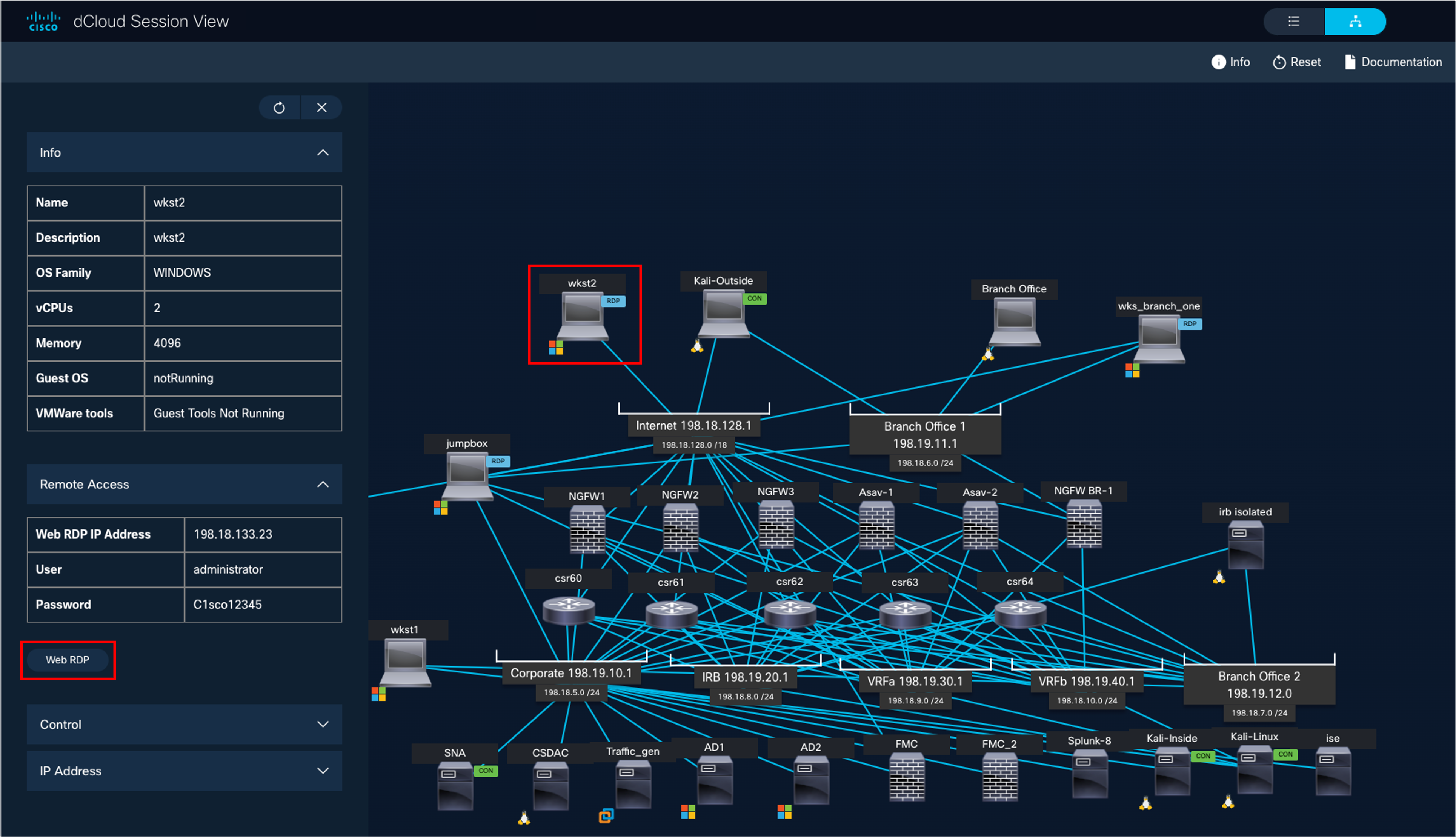
Lab Topology

Task 1 - Verify the connectivity to inside network
-
Open remote desktop to wkst2. We will use this workstation to RAVPN to the firewall.
-
Open the AnyConnect client (Go to Windows > Cisco > Cisco AnyConnect Secure Mobility Client) and connect to NGFW1 (the profile and NGFW1 information is pre-populated)
-
Use the following credentials:
- Username: engineeringuser
- Password: C1sco12345
-
-
Open the command prompt and ping 100.100.100.1
Task 2 - Explore the RAVPN Dashboard
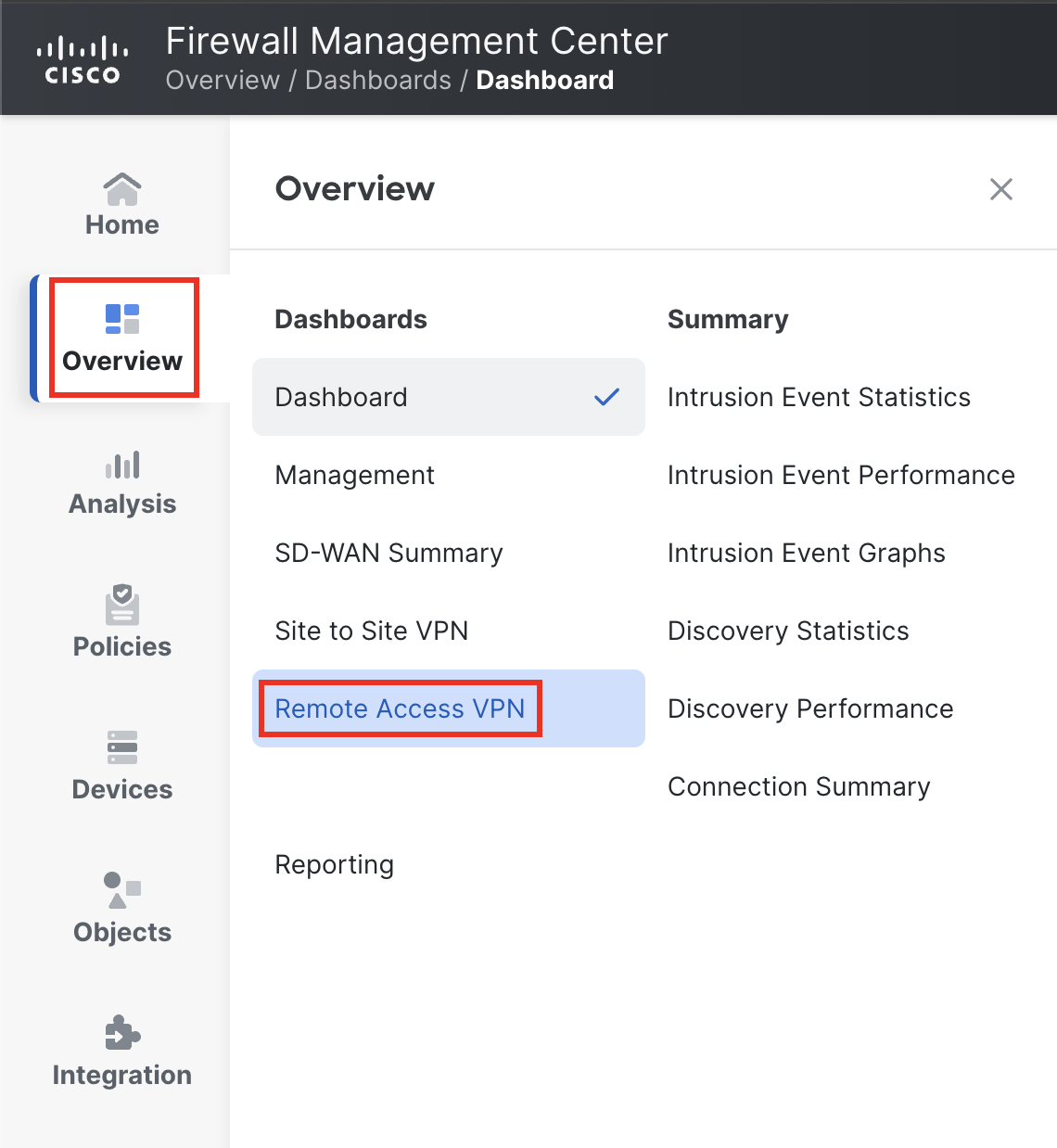
Navigate to the RAVPN dashboard, Overview > Dashboards > RAVPN.
We already connected to the VPN so should have at least one session on the RAVPN dashboard.
Note
The Active Sessions information might not be visible instantly. It can take up to five minutes to refresh. Alternatively, you can use the refresh button in the upper-right to refresh instantly.
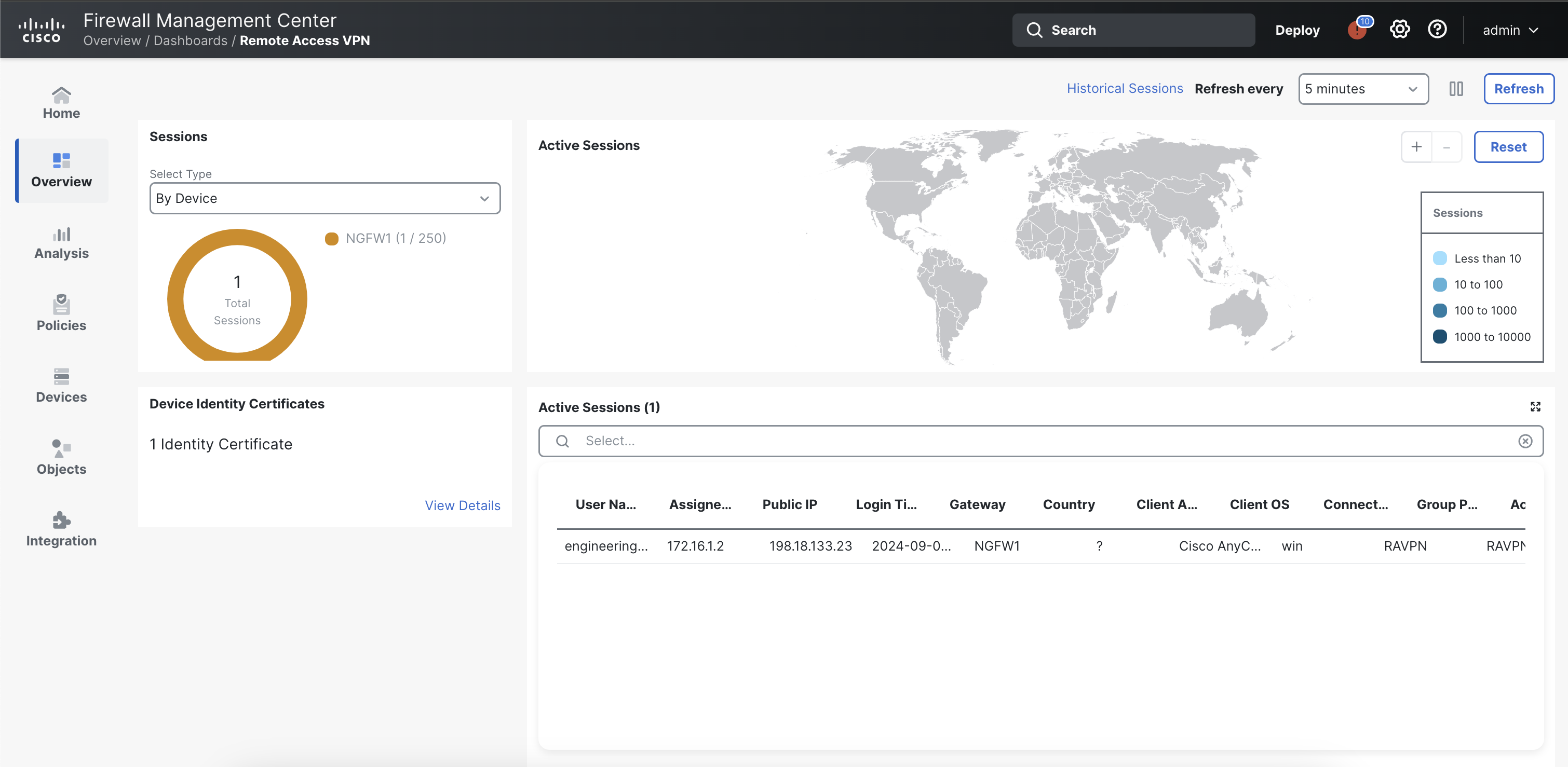
As seen above, the RAVPN (Remote Access VPN) Dashboard feature in Cisco Firepower Threat Devices provides a comprehensive view of active VPN sessions, allowing administrators to monitor and manage remote connections securely. The Active Sessions pane displays crucial details such as user names, connection duration, and data transfer statistics. As an admin, you can choose to terminate any sessions whichever way you like.

Moreover, the ability to track the location of VPN connections adds an extra layer of security and insight into network activities. In instances where location tracking is not applicable, as in the case of a VM without specific location information configured, the dashboard remains a valuable tool for monitoring user activity and ensuring the integrity of the VPN environment. However, in this particular case, we can't see any such information because this is a Virtual Machine (VM) deployed with no location-specific details configured.
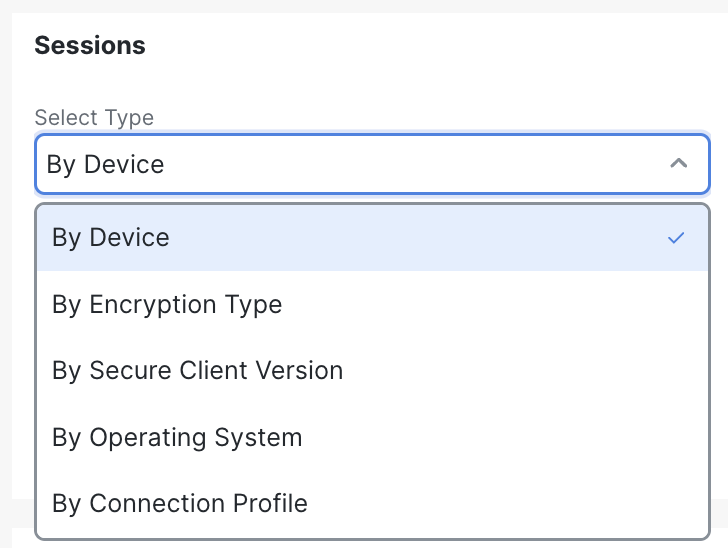
Under the Sessions on the left pane, you have the option to filter VPN sessions based on Devices, Encryption Type, Secure Client Version, etc. For example, This can help filter the users who are maybe using a out-dated version of Secure Client to connect to version. The admin then has the power to terminate their session and notify them to update their software version.
In conclusion, the RAVPN Dashboard stands as a pivotal tool for network administrators using Cisco Firepower Threat Devices, offering real-time visibility into active VPN sessions. While the absence of location-specific information in certain instances may limit certain insights, the overall capabilities of the dashboard remain robust. Administrators are encouraged to leverage the full potential of this feature by ensuring proper configuration, thereby enhancing their ability to monitor, manage, and secure remote access effectively in diverse network environments.
Tell us how we are doing
We are doing our best to ensure the scenarios in this lab guides are useful, clear and work as expected.
Please share your thoughts to help us improve or fix any problems you may run into..
Click here to provide your feedback or report an issue with this guide
Updated about 1 year ago