EVE Exception List
Introduction
Introduced in release 7.3, Encrypted Visibility Engine (EVE) identifies client applications and processes that utilize TLS encryption. It enables visibility and allows administrators to take action and enforce policy within their environments.
In release 7.4, enhancements were added to EVE to block malicious traffic based on threat score. Administrators can adjust the threat score required for EVE to block potentially malicious traffic. This means that as EVE analyzes traffic, it assigns a score based on the probability that the traffic is malware. If the incoming traffic is deemed to be malicious, then based on the threat score, EVE can be configured to block the connection.
However, scenarios like Internal Penetration Testing can create a need to bypass EVE's block verdict. Hence, in release 7.6, an EVE Exception List has been introduced which aims to ensure the continuity of connections and services when EVE’s block feature is enabled.
Configuration
The EVE Exception List allows customers to bypass EVE’s verdict for blocking a connection based on the below attributes:
- Process Name
- Destination IP Address
The configuration of the EVE Exception List can be done in two ways - proactively and reactively.
Proactive EVE Exception List
- Navigate to Policies > Access Control. Click on the Edit icon of the Access Control Policy to be edited.
- Go to More > Advanced Settings. Click on the Edit icon against Encrypted Visibility Engine.
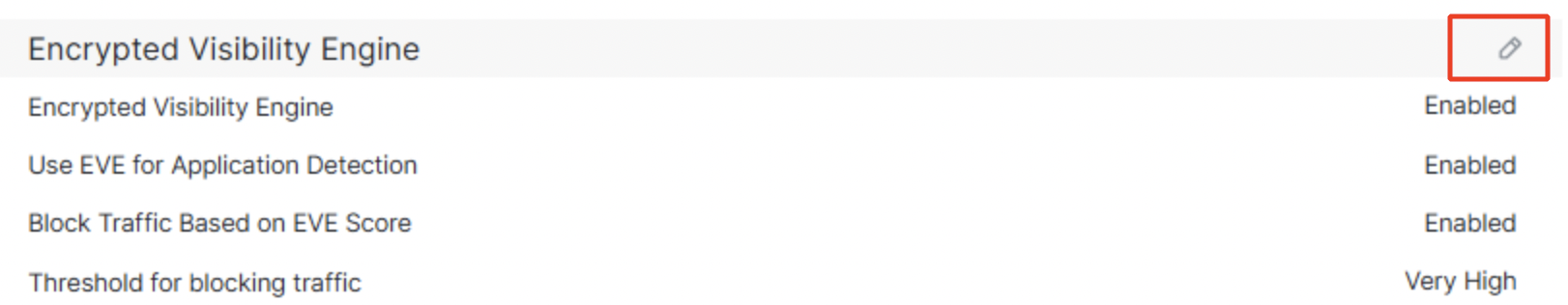
Encrypted Visibility Engine settings
- Ensure that the below sliders are turned on:
i. Recommended Settings
ii. Encrypted Visibility Engine (EVE)
iii. Use EVE for Application Detection
iv. Block Traffic Based on EVE Score
The block threshold configured in the below example is Very High, which means that traffic detected as malicious with Encrypted Visibility Threat Confidence Score 99% and above will be blocked. To add an exception to this block verdict, click on Add Exception Rule.
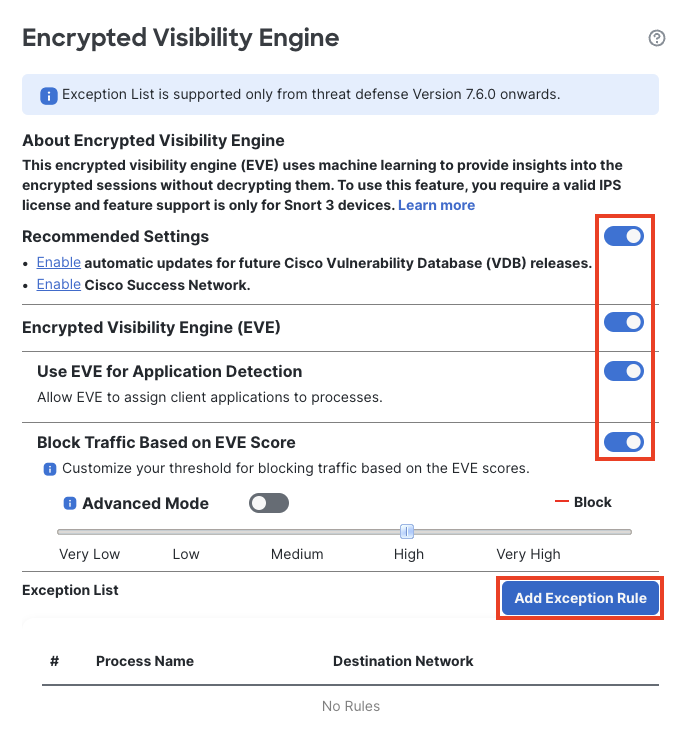
Encrypted Visibility Engine settings
- Navigate to the tab Process Name. Type in the Process Name and click on Add to Process.
Note that the Process Name should exactly match the EVE Process Name seen in Unified Event Viewer. It is both case and space-sensitive.
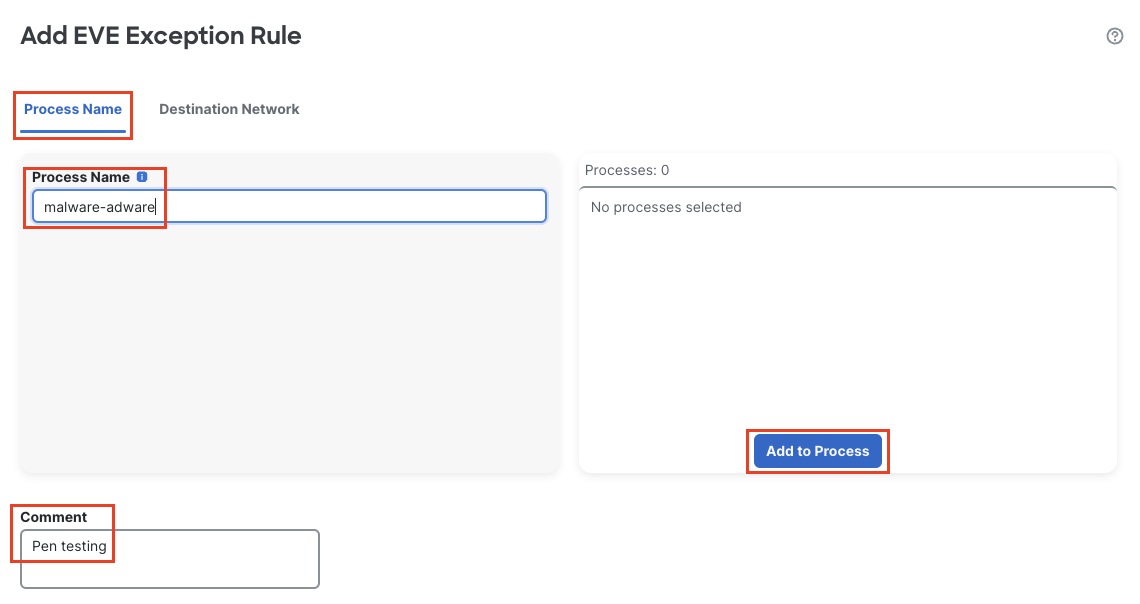
Process Name under EVE Exception Rule
- Navigate to Network Objects. Against Manually Enter IP, type in the destination IP address to be exempted from EVE block. Click on the + sign to add it. Comments can be added in the Comment box for the EVE Exception Rule. Click on Save.
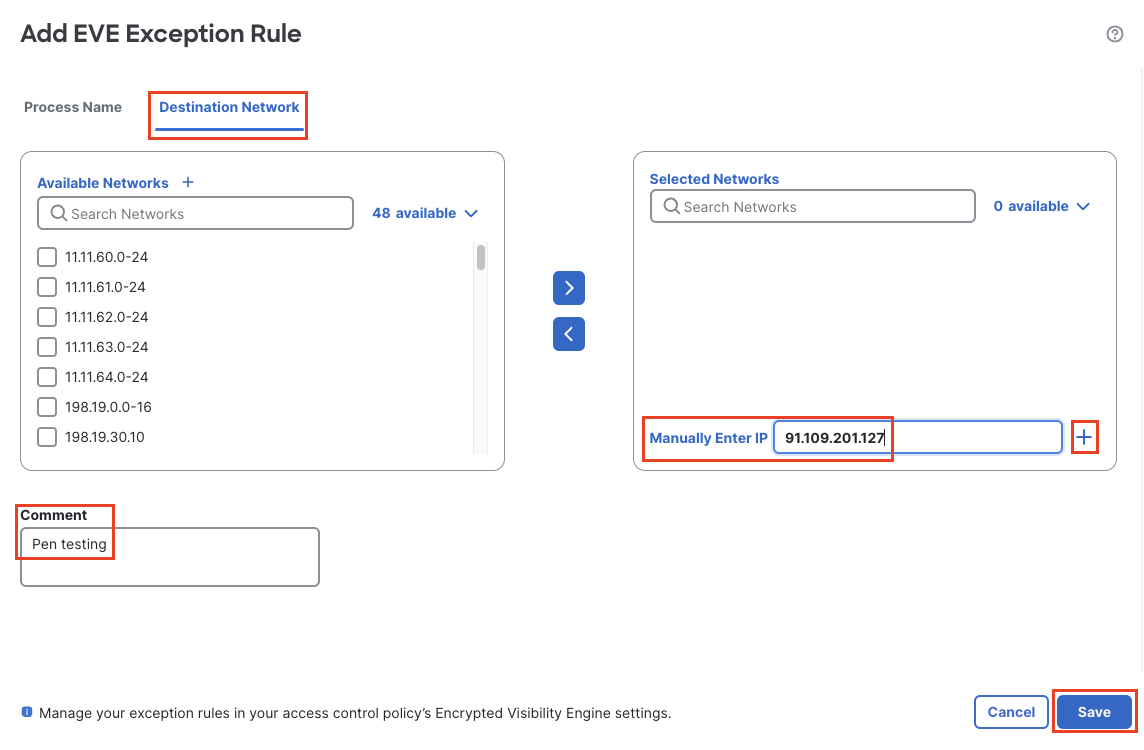
Network Objects under EVE Exception Rule
- The Exception Rule gets added as shown below. Click on OK.
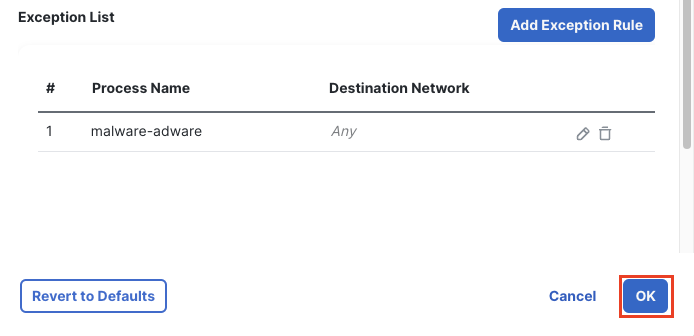
EVE Exception Rule
- Click on Save to save the changes to the Access Control Policy and click on Deploy to deploy the changes to the firewall.
- Navigate to Analysis > Unified Events. In the search bar filter with the values configured in the exception list -- i.e. for the columns Encrypted Visibility Process Name and Destination IP. Click on > against the event to expand it.
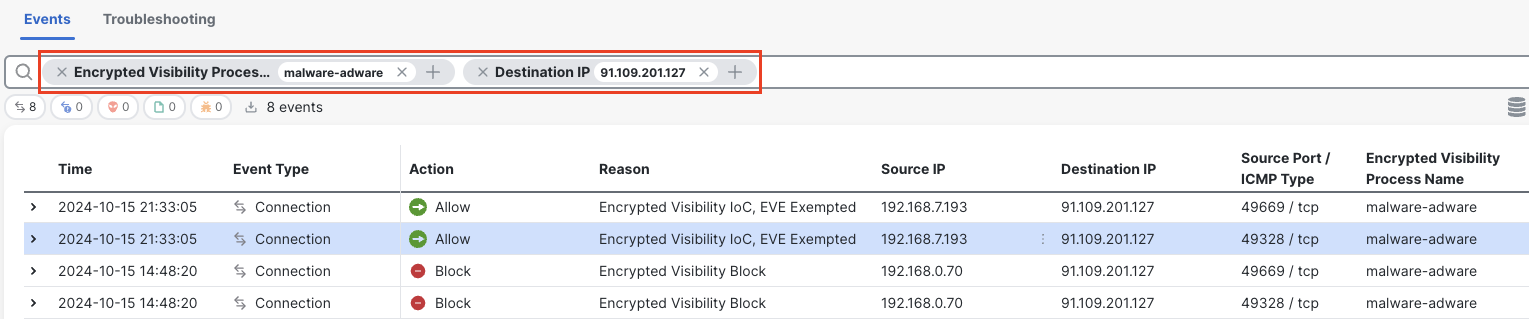
EVE Exempted traffic in Unified Event Viewer
- Note that the traffic has been allowed even though EVE detected it as malicious with Encrypted Visibility Threat Confidence Score equal to 100%. The Reason is seen as EVE Exempted.
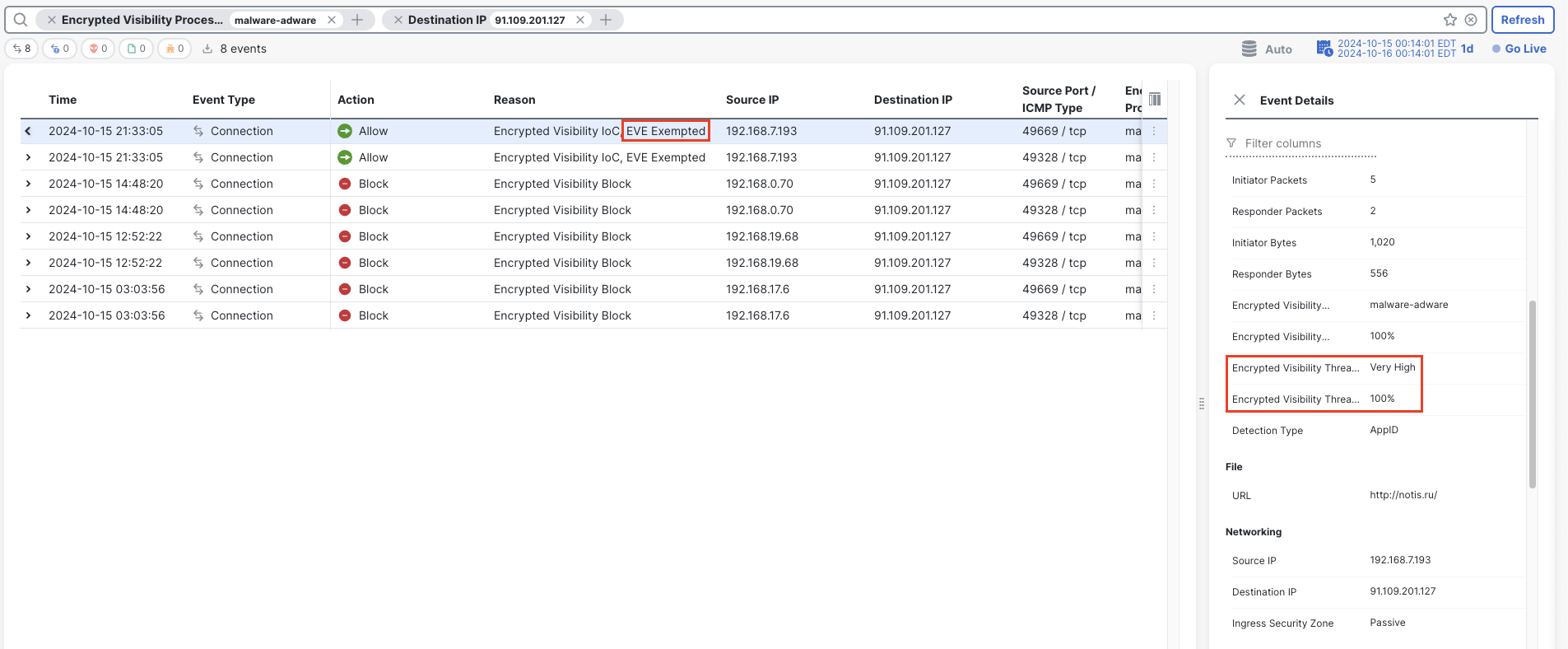
EVE Exempted traffic in Unified Event Viewer
Reactive EVE Exception List
- Navigate to Analysis > Unified Events. In the search bar filter with Reason: Encrypted Visbility Block to view all the traffic blocked based on EVE block threshold.
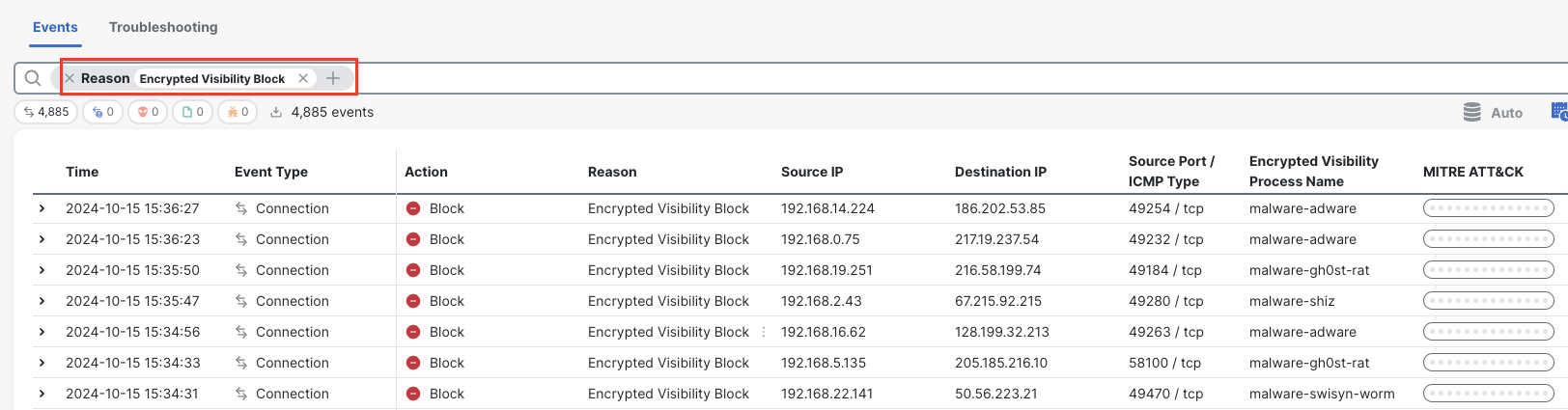
EVE Blocked traffic in Unified Event Viewer
- Click on the three dots against Encrypted Visibility Block for the event that needs an exemption from the EVE block verdict. Click Add EVE Exemption Rule.
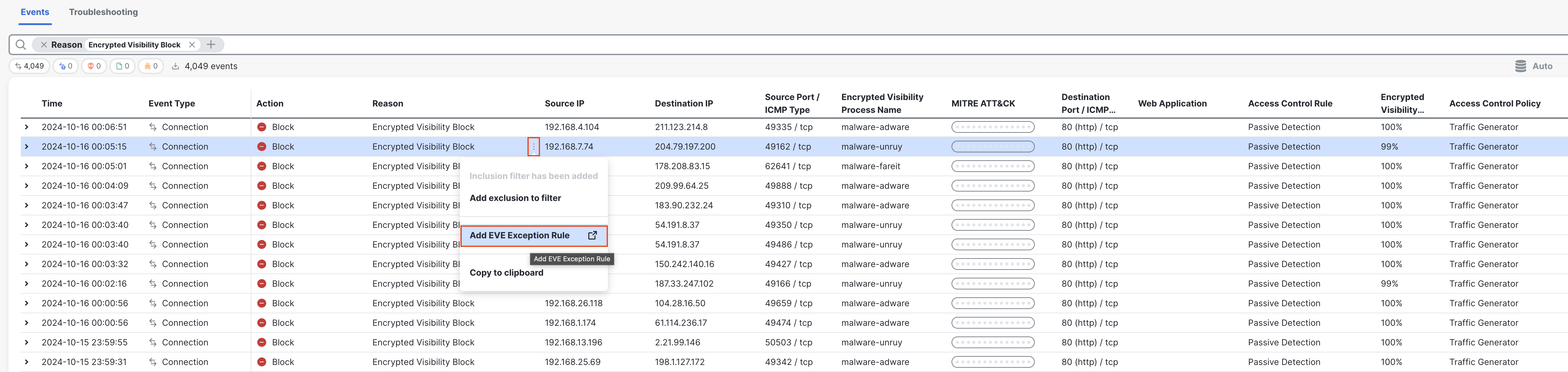
Adding EVE Exception Rule from Unified Event Viewer
- This opens the Encrypted Visibility Engine settings page under the Access Control Policy mapped to the Device, with the newly added rule at the bottom of the EVE Exception List.
Click on Save to save the Encrypted Visibilty Engine and then on Save on the top right corner to save the changes to the Access Control Policy. Click on Deploy to deploy the changes to the firewall.
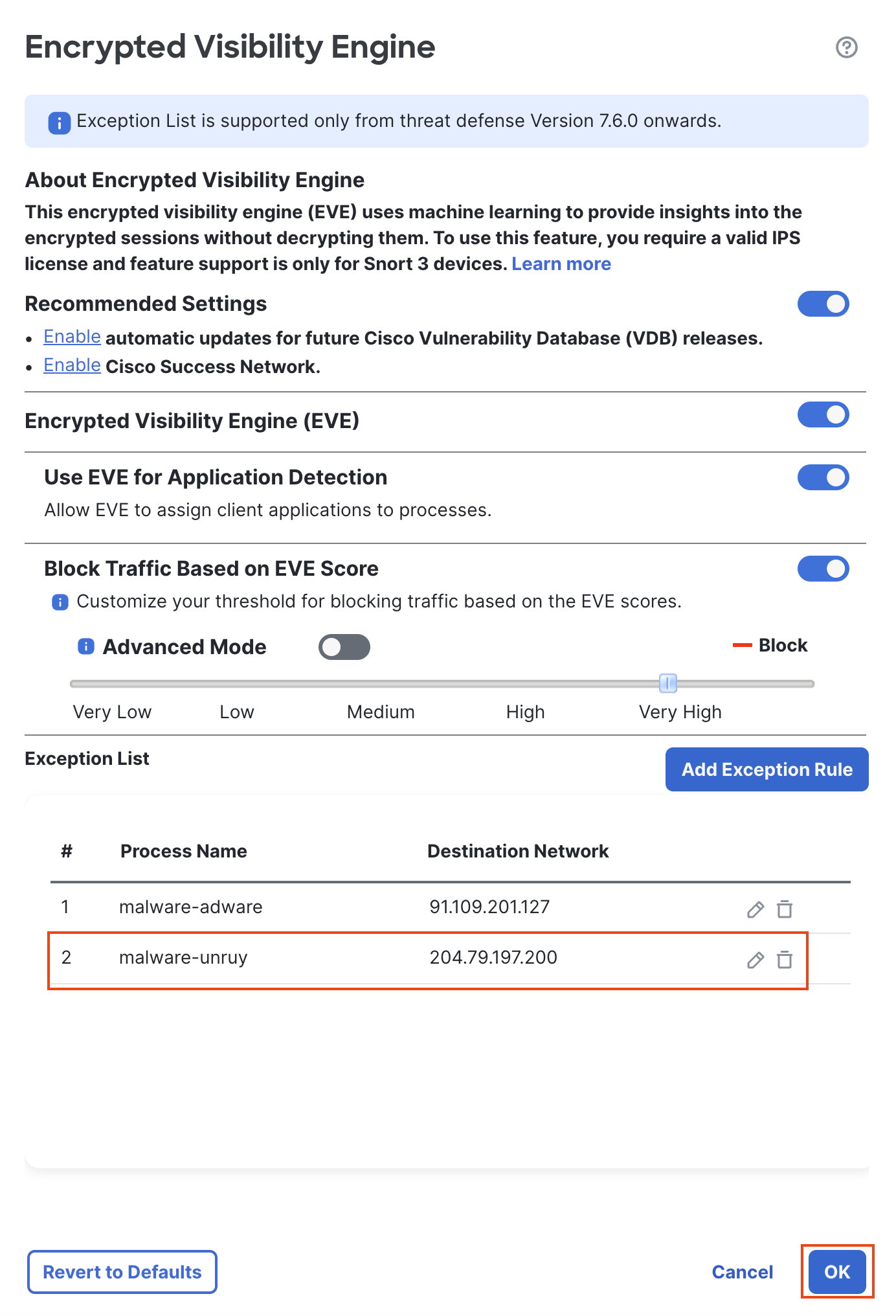
EVE Exception rule added automatically
- Go back to Analysis > Unified Events. In the search bar filter with the values in the exception list i.e. the columns Encrypted Visibility Process Name and Destination IP. The exempted event is now allowed through the firewall with the Reason: EVE Exempted.
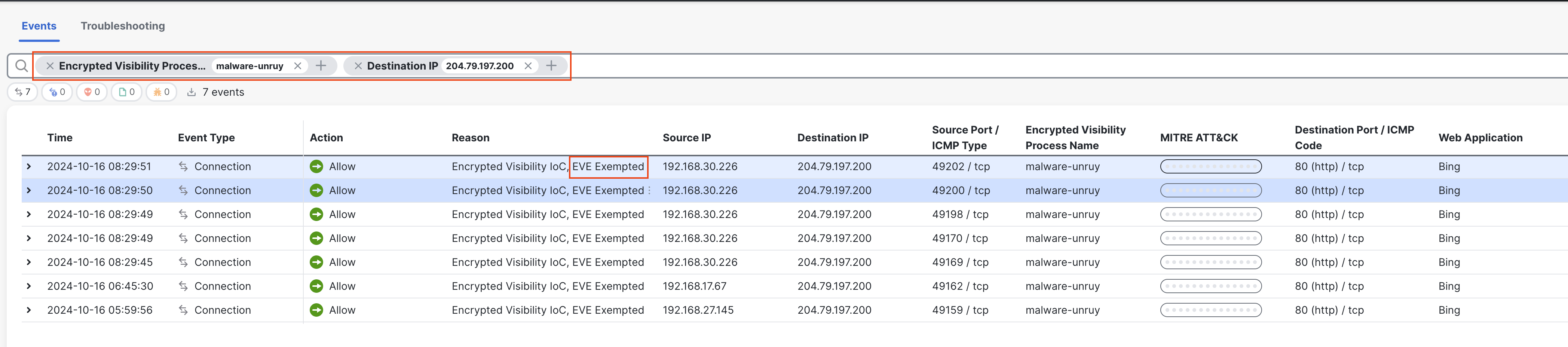
EVE Exempted traffic in Unified Event Viewer
Summary
With EVE Exception List, trusted networks and penetration testing scenarios can be easily exempted while continuing to block other malicious traffic with Encrypted Visibility Engine.
Updated 11 months ago
