Scenario 13 - Access Control Rules
At last we are at the point of creating the firewall rule set. We will create a few example Access Control rules to illustrate the capabilities. The actual rule set will vary greatly depending on the device deployment use-case. For an inline IPS you might only have a handful of rules while for a large edge firewall the rule count may be in the thousands.
Lab Tasks
These are the tasks in this scenario. If you are familiar with the Secure Firewall you may do these on your own, or for step-by-step instructions see below.
- Task 1 - Create a rule to block outbound connections to China and the Russian Federation
- Task 2 - Create a rule to block applications with a Very High Risk and Very Low Business Relevance
- Task 3 - Create a rule to block malicious, malware and pornography websites
- Task 4 - Add the custom Intrusion policy, variable set and File and Malware policy to inspect all allowed connections
- From the FMC2 web UI, open the NGFW1 policy. The rules page will load by default or you can click Access Control in the packet flow depiction near the top.
There are two views in the new UI layout. Clicking the grid button shown below switches between the two rule views.
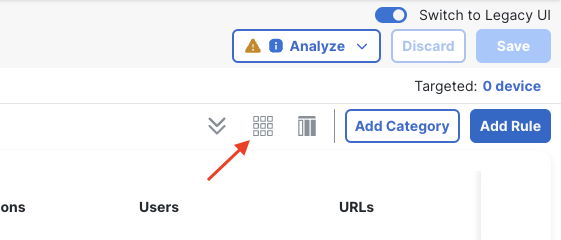
Rule View Selector
The column button to the right allows you to show or hide columns.
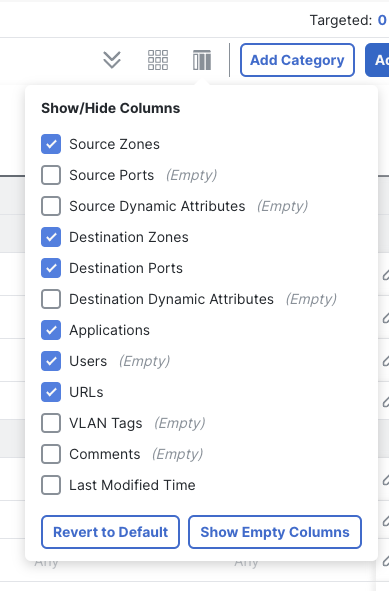
Show/Hide Columns
Notice there are several default rule categories. Each policy has a Mandatory and a Default rule category. Additional categories can be added as desired. Because this is a child policy we see the Global Parent rule categories as well.
Rules in the Global Parent policy Mandatory category are evaluated before any rules in the NGFW1 policy. Also, rules in the Default Global Parent category are evaluated after any rules in the NGFW1 policy and before the Default Action.
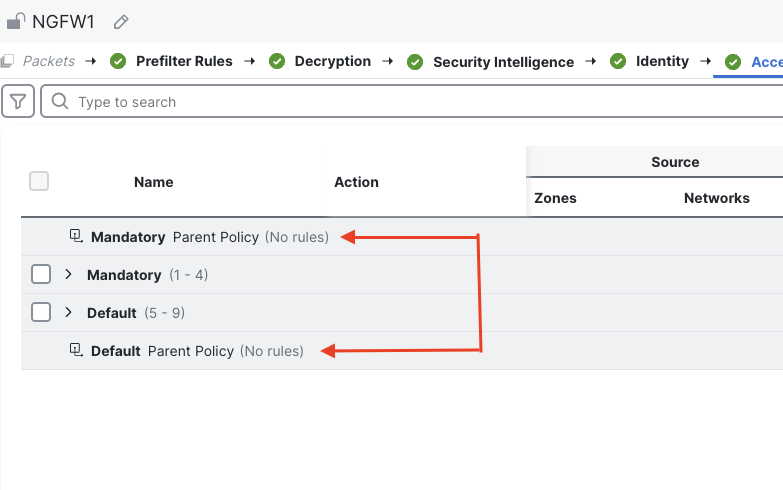
Global Parent Categories
Our policy will deal with outbound traffic only. We will create several rules to control outbound connections, our goals are:
- Log all connection events to the Splunk syslog server but not to the FMC
- Log any blocked connections to the FMC and the Splunk server
- Block connections to specific geolocations
- Block connections to URL categories
- Block connections for specific applications
- Inspect all allowed traffic using Snort as well as check for malware files
-
At the bottom, click the Default Action drop-down.
The default is to use the Global Parent default action.
Change this to Access Control: Block All TrafficClick the gear icon to the right of the drop-down.
Check the Log at beginning of connection and Syslog server boxes.
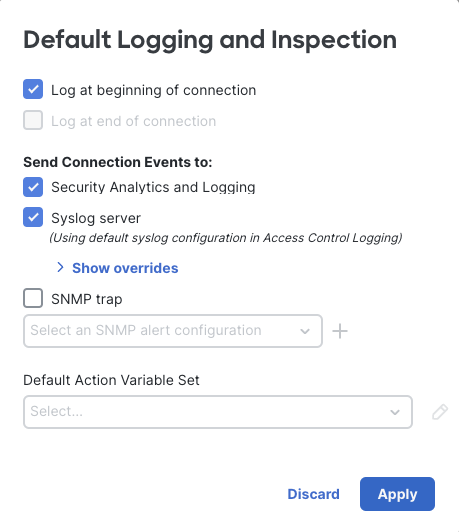
Default Action Logging
Click Apply to save changes.
Notice that we only have the option to log at the beginning of the connection. This is true for all block rules as the beginning of the connection is also the end.
Task 1 - Geolocation Block Rule
- Click the Add Rule button
Name the rule Geolocation Block
Action: Block with reset
Logging: Log at beginning of connections check Syslog server
Zones tab
Add OutZone to the destination zone
Networks tab
Select the Geolocations tab
Add China and Russian Federation to the destination networks. Click Apply.
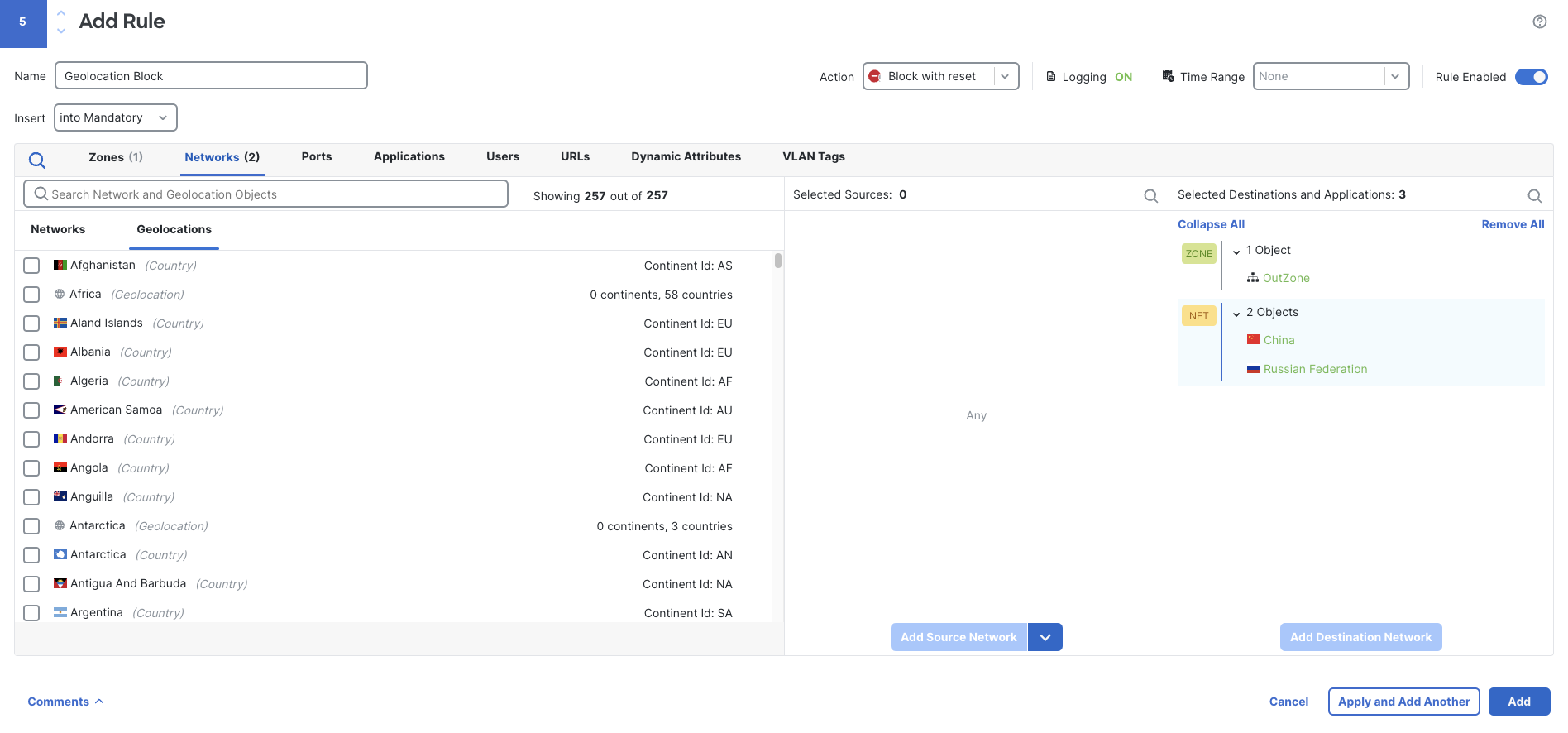
Geo Block Rule
Task 2 - URL Block Rule
- Following the procedure above to create a rule named Block URL Categories. Add a rule to block connections to the following URL Categories:
- Malicious Sites
- Malware Sites
- Pornography
Include the same destination zone and logging options as the previous rule.
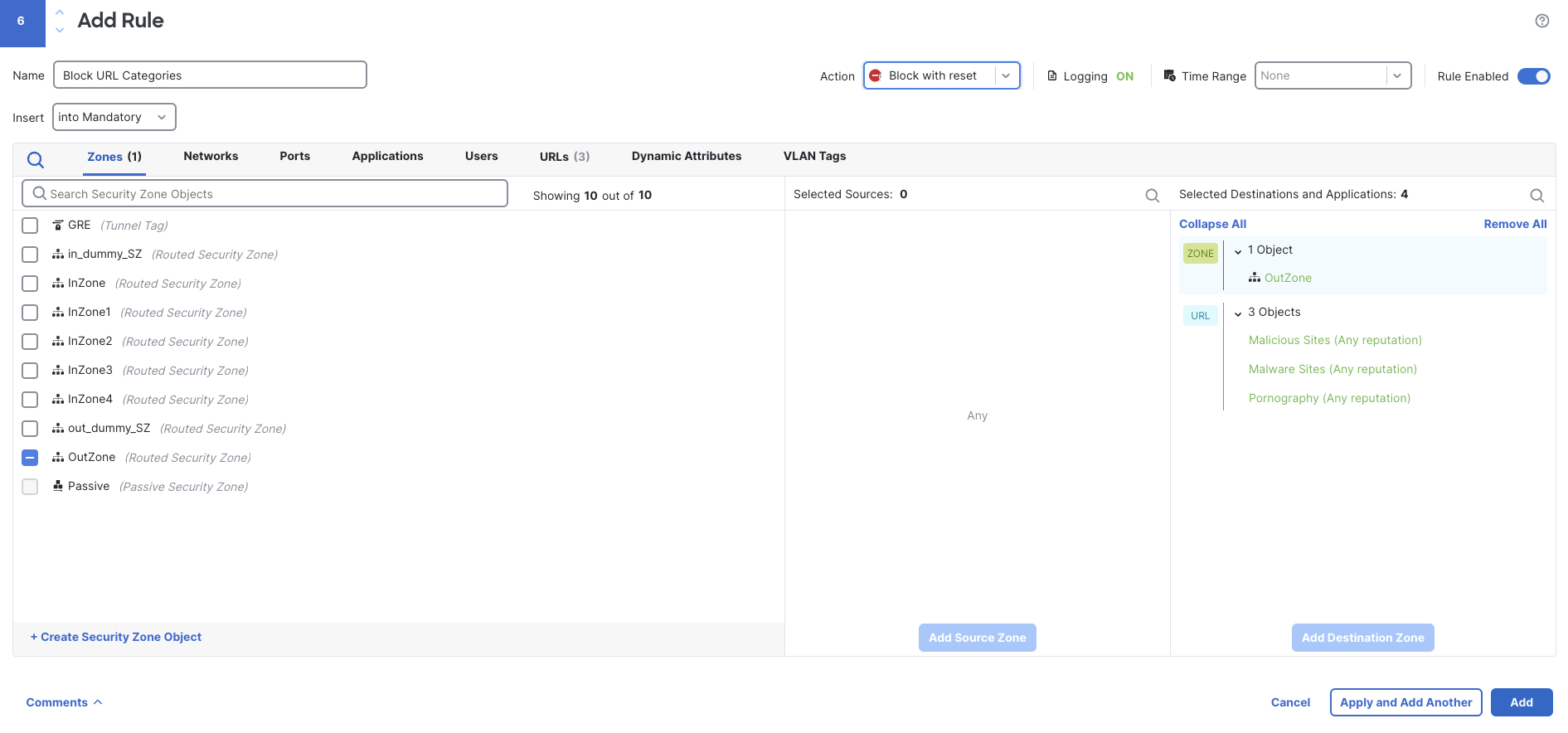
URL Category Block Rule
Task 3 - Application Blocking Rule
- Create a rule named Blocked Applications.
Configure the rule as above regarding zones and logging.
Block applications with a Very High Risk and Very Low Business Relevance.
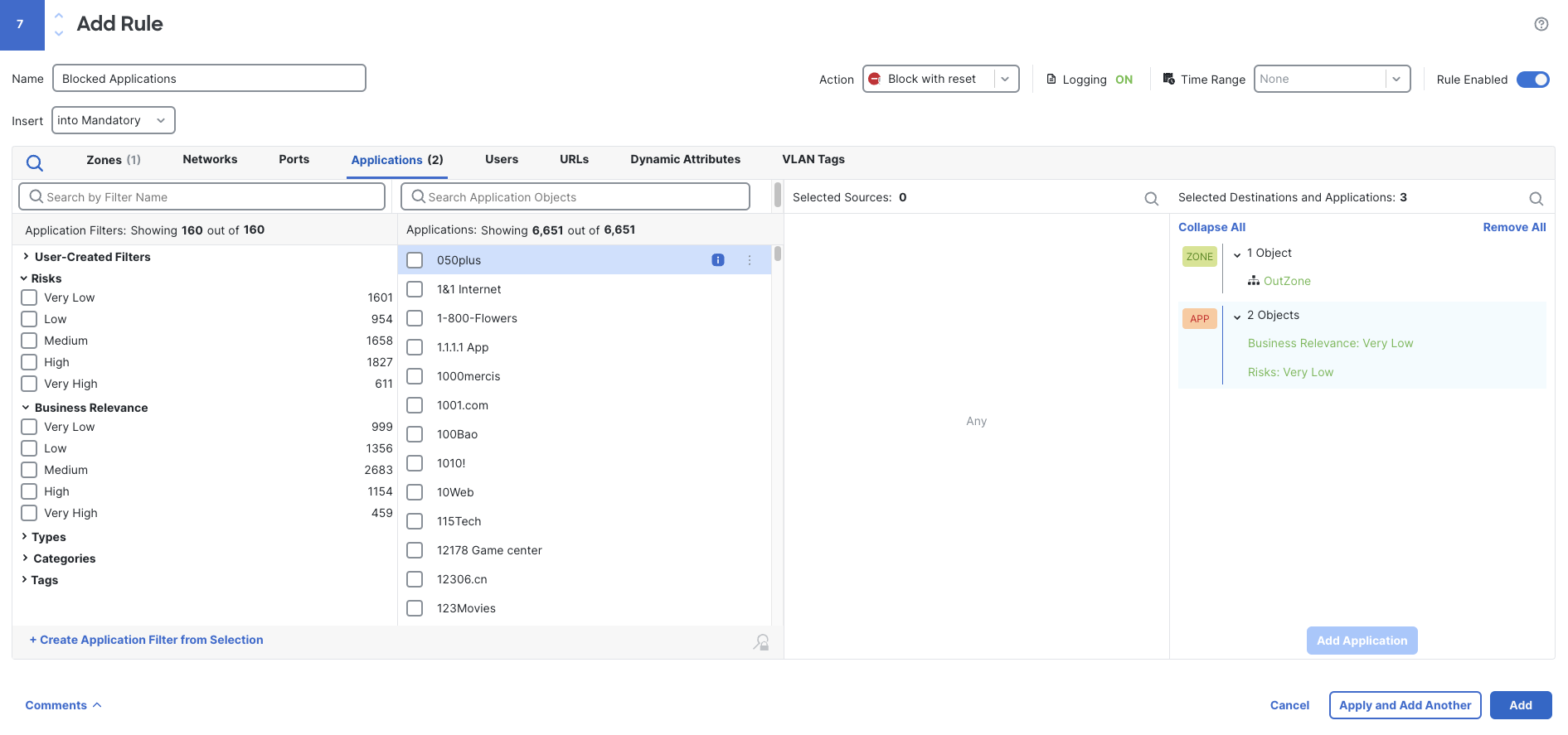
Business Relevance Block Rule
Task 4 - IPS and Malware Inspection
-
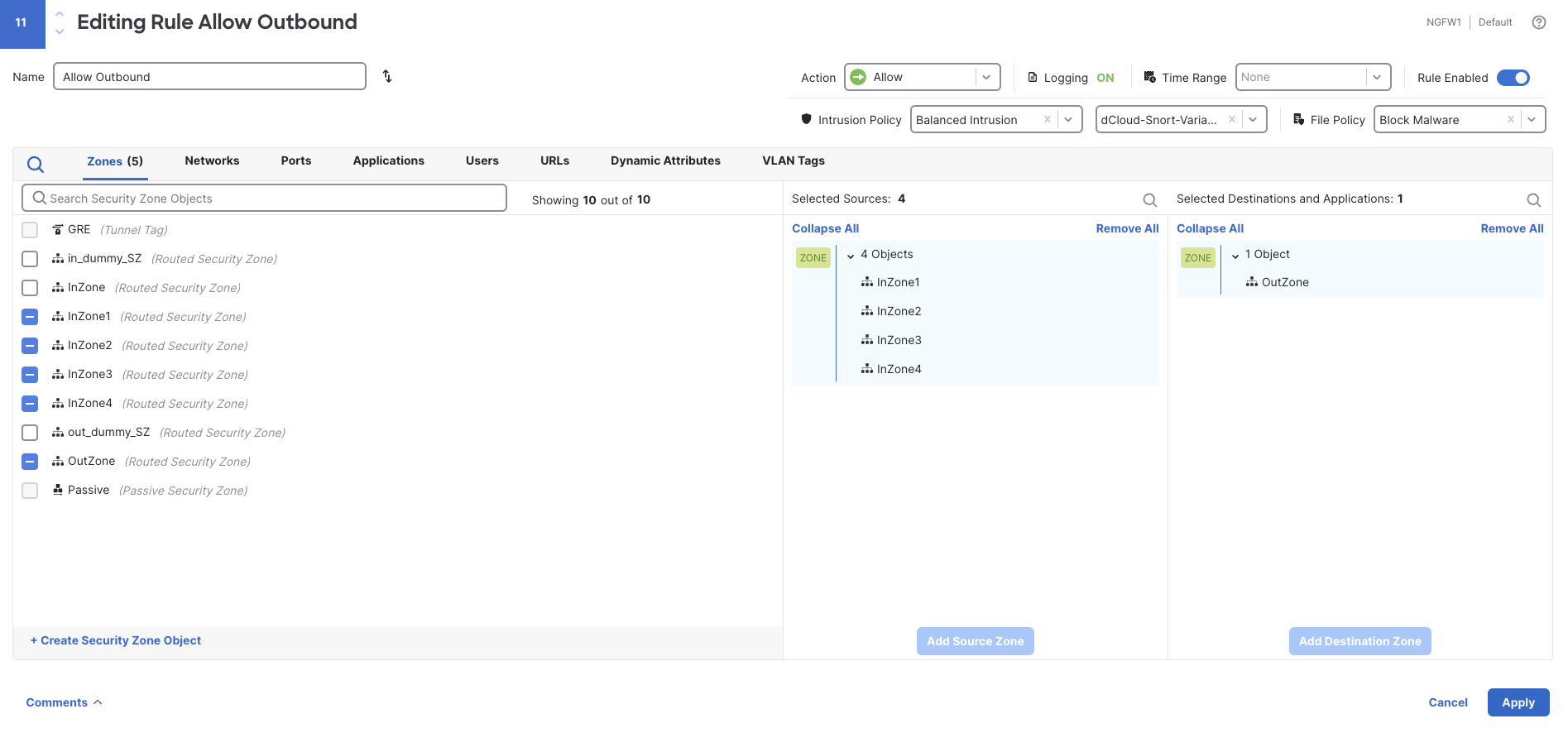
Edit the Allow Outbound rule
Set the Intrusion Policy to the user created Balanced Intrusion policy.
Use the dCloud-Snort-Variables Variable Set
Set the File Policy to Block MalwareSet the log settings to log connection events at the end of the connection to the Syslog server only and not the FMC.
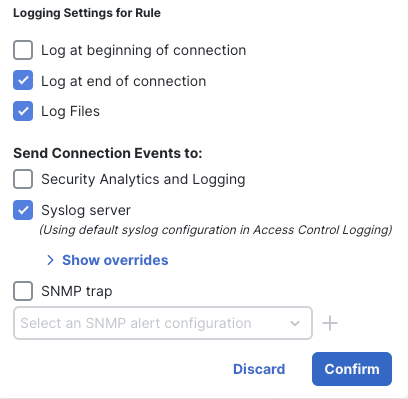
Allow Outbound Logging Settings
Note, the logging settings here control connection and file events. Intrusion and malware events will always be logged to the FMC in addition to any additional logging configured in the policy Logging settings. In addition to this, connection events associated with a malware or an intrusion event will also always be logged to the FMC.
- As we added rules we did not pay attention to the rule order. Because we have a small rule set it will be easy to drag the rules into the desired order. However, with a larger rule set, it would be better to specify the rule position as the rule is created.
Click and drag the rules in your policy into the order below. Keep all your rules in the Mandatory category.- Geolocation Block
- Block URL Categories
- Blocked Applications
- Allow Outbound
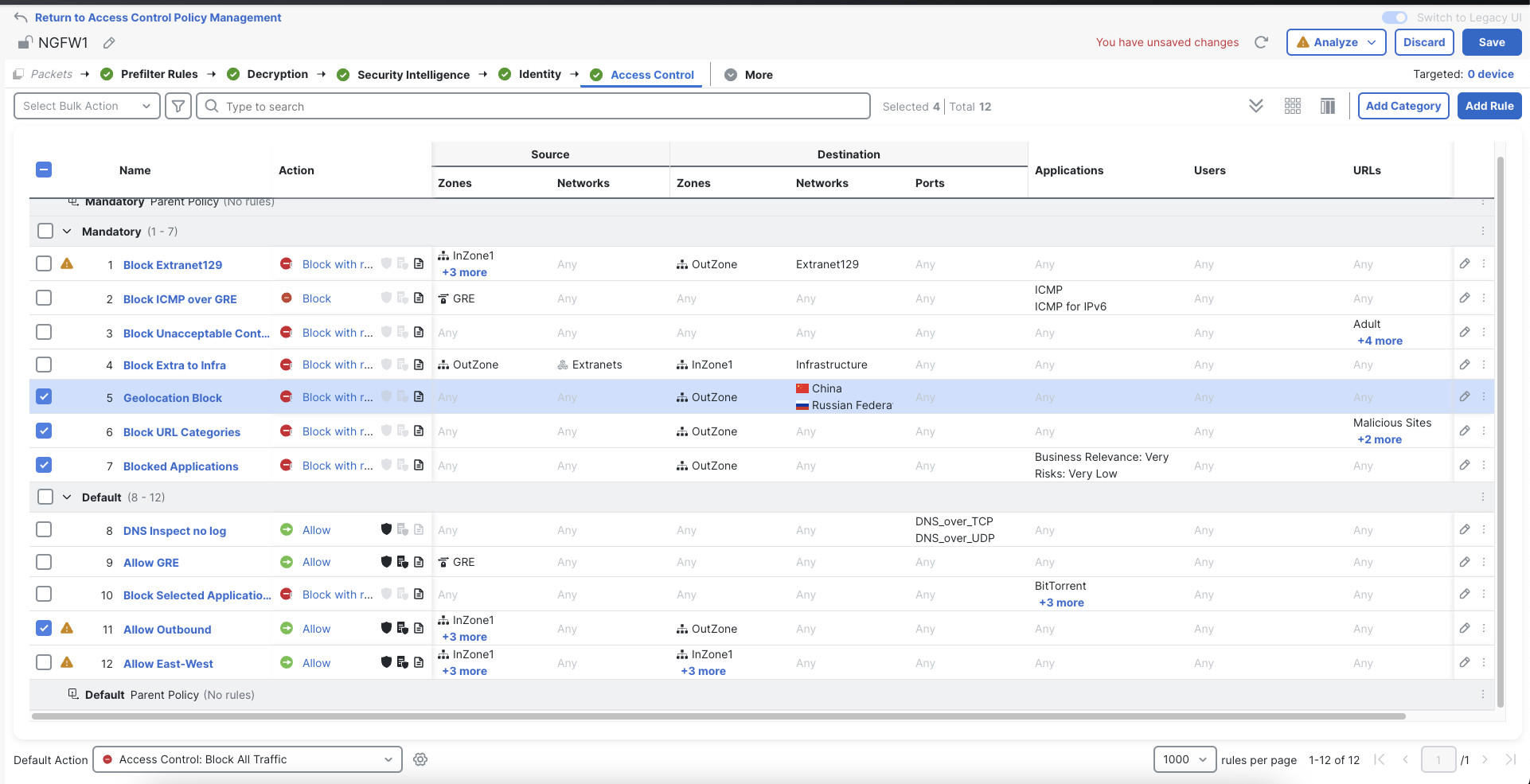
Completed Access Control Policy
Save your Access Control policy and then use the Deploy option in the menu to deploy your policy changes to the NGFW1 device.
Tell us how we are doing
We are doing our best to ensure the scenarios in this lab guides are useful, clear and work as expected.
Please share your thoughts to help us improve or fix any problems you may run into..
Click here to provide your feedback or report an issue with this guide
Updated about 1 year ago