Scenario 8 - Network Discovery
Up to this point, we have been configuring the basic routing and setup of the environment. Now we will take a closer look at the threat features of the Secure Firewall. Network Discovery builds the FMC host database based on passive traffic analysis. The Network Discovery policy defines the networks the system uses to collect this host, user and application data and should correspond to the internal or protected networks.
Lab Tasks
These are the tasks in this scenario. If you are familiar with the Secure Firewall you may do these on your own, or for step-by-step instructions see below.
- Task 1 - Add a rule to discover hosts, user and applications for the IPv4 RFC-1918, Corp-LAN and Branch-LAN networks
- Task 2 - Deploy policy changes and note the new hosts detected in the FMC host database
Task 1 - Add Discovery Rules
-
On the FMC2 web UI, navigate to Policies -> Network Discovery
Notice there is an existing App ID rule for all IPv4 and IPv6 networks. -
Click + Add Rule to add a rule to the policy. Network Discovery rules are unordered so the position within the policy does not matter.
We will add our internal dCloud lab range as well as the RFC-1918 IP ranges.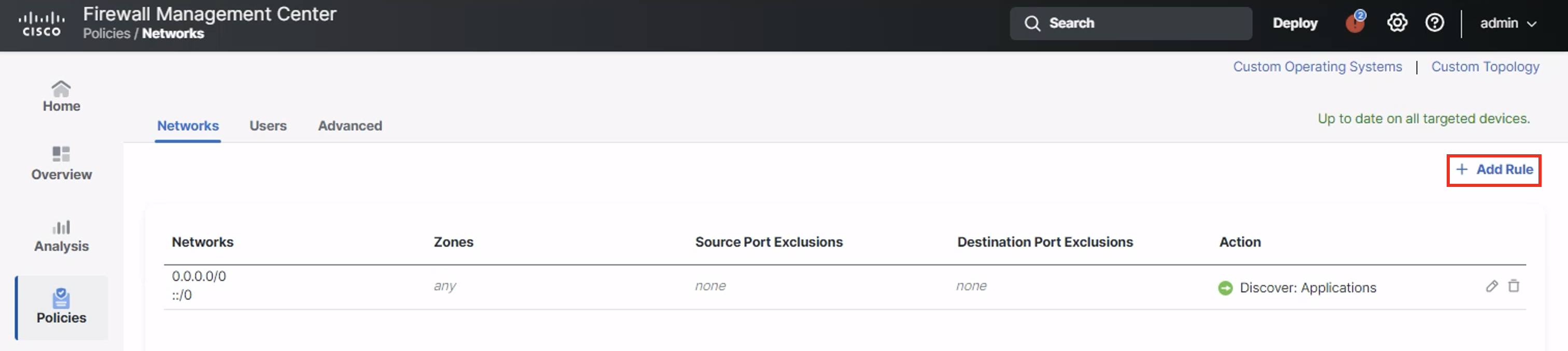
From Available Networks add the IPv4-Private-All-RFC1918, Corp-LAN and Branch-LAN objects to the rule.
The rule action should be Discover. Check Hosts, Users and Applications
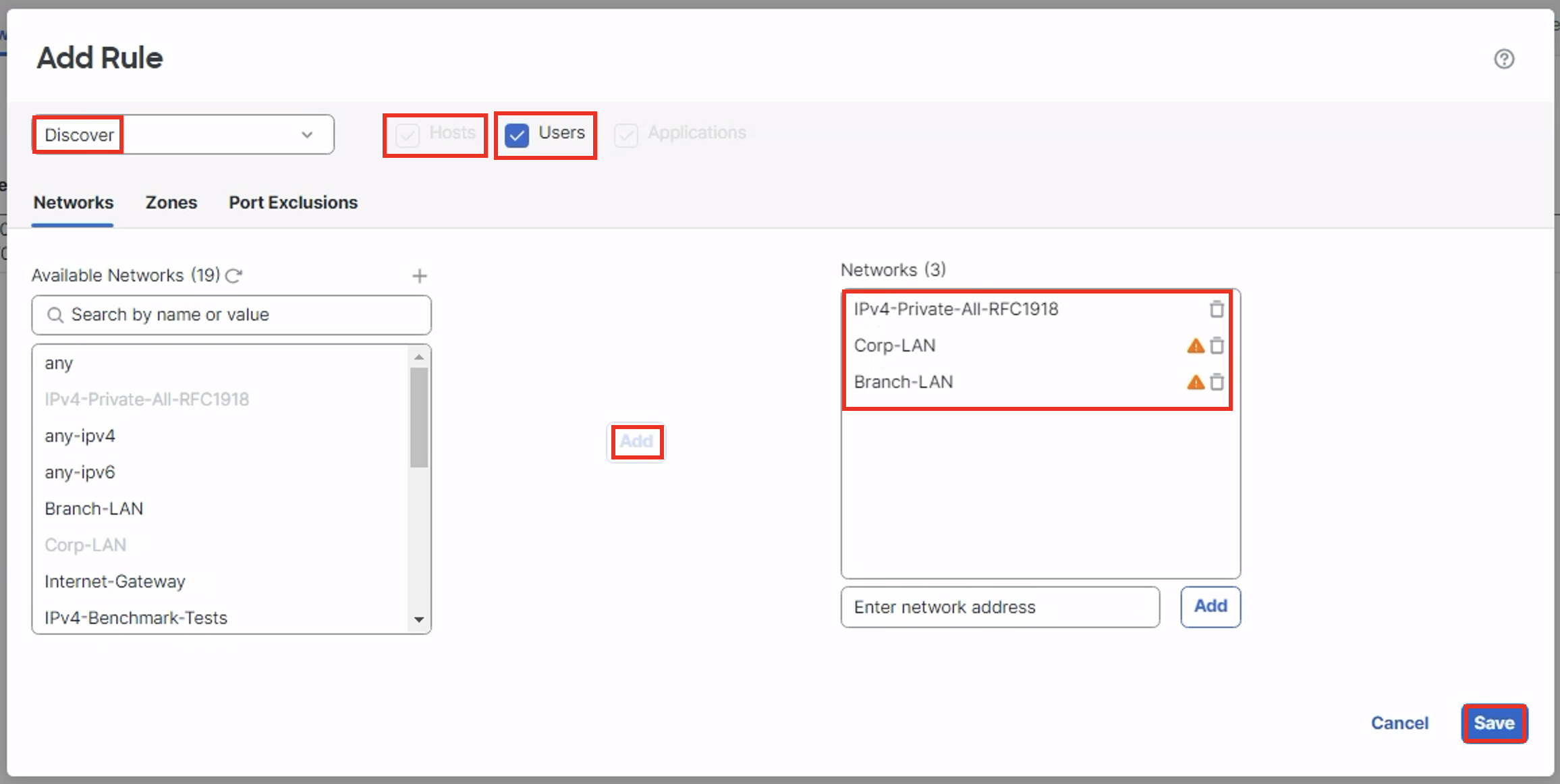
Click Save to save the rule.
Warning
The below warning is seen while adding Corp-LAN and Branch-LAN and while checking ‘Users’:
Click Proceed.
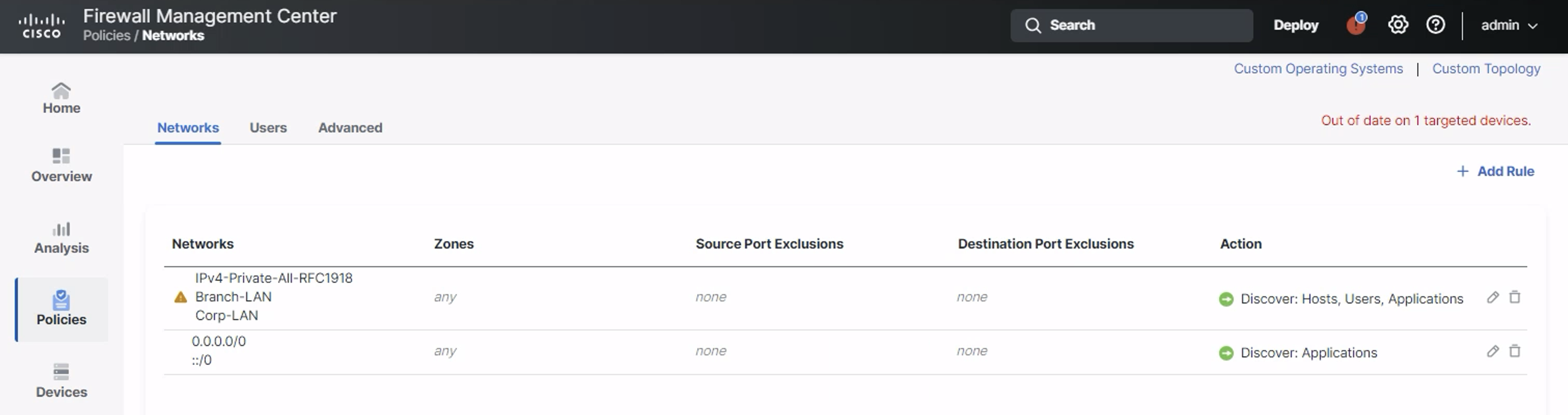
Your Discovery policy should look like the one in the figure below.
- Navigate to Analysis > Hosts > Network Map and note that there are no hosts in the database.
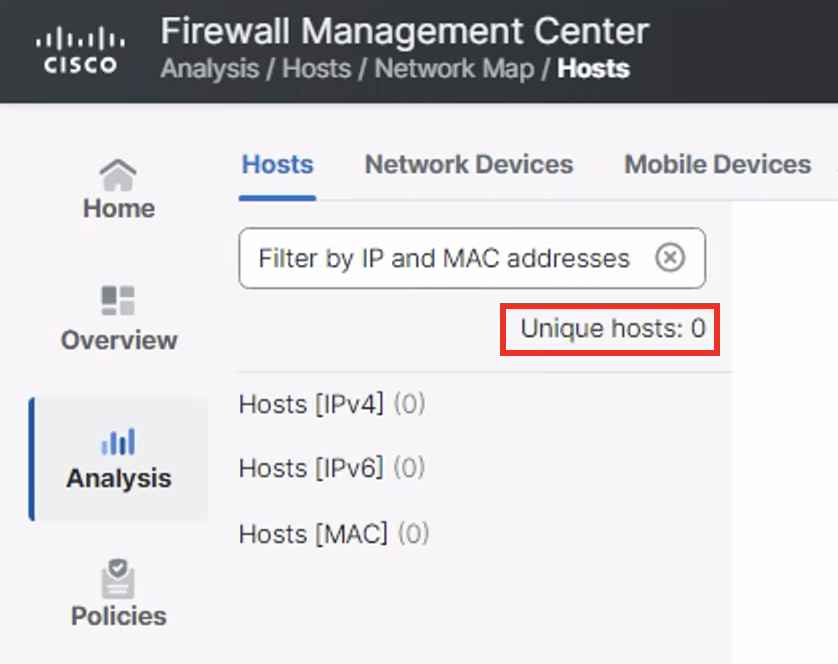
Empty Host Database
Task 2 - Deploy Changes and Test
-
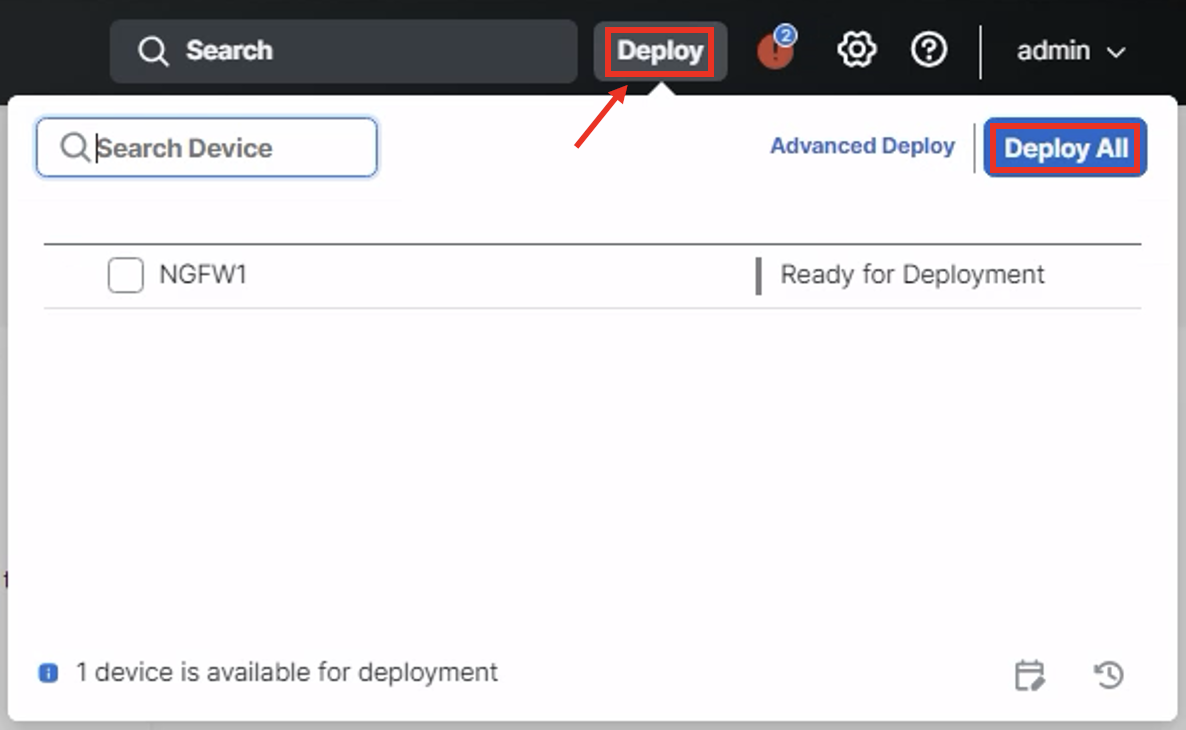
Click Deploy in the top menu and deploy changes to NGFW1.
Once the deployment is finished, refresh the Hosts screen. You should see these numbers start increasing with each page refresh as hosts are passively added to the database.
To view a host entry, expand the tree on the left and click on one of the discovered IP addresses.
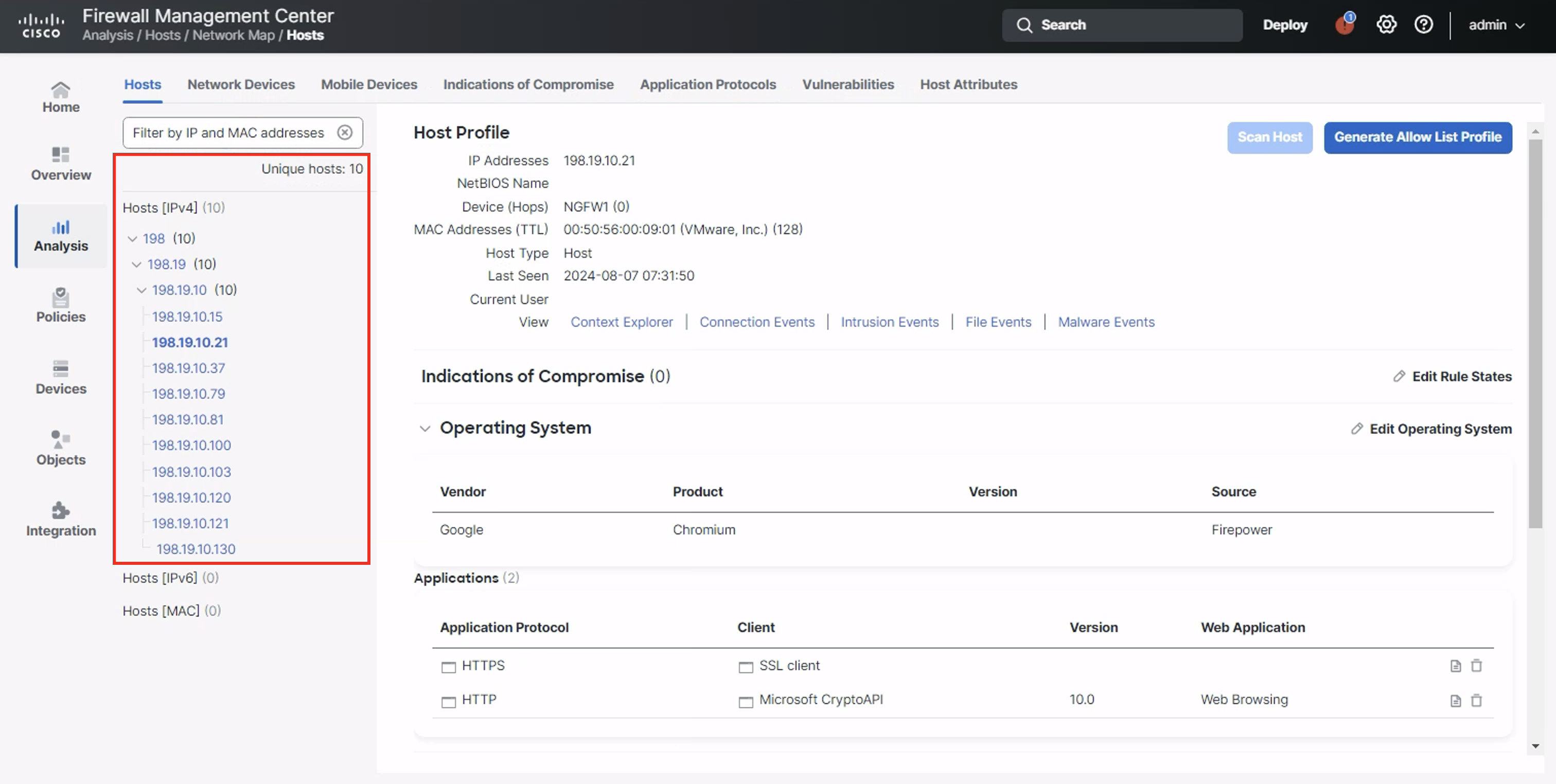
Host View
Host count and accuracy will increase over time as the system process more traffic.
Tell us how we are doing
We are doing our best to ensure the scenarios in this lab guides are useful, clear and work as expected.
Please share your thoughts to help us improve or fix any problems you may run into..
Click here to provide your feedback or report an issue with this guide
Updated over 1 year ago