Scenario 9 - Malware & File Policy
In this scenario we will create a Malware & File policy to be used later with Access Control rules. We will configure the policy to block malware files as well as blocking executable files from being downloaded via HTTP. Note that this will also work for HTTPS if we implement TLS decryption.
Lab Tasks
These are the tasks in this scenario. If you are familiar with the Secure Firewall you may do these on your own, or for step-by-step instructions see below.
- Task 1 - Create a new Malware & File policy
- Block malware for all supported protocols and file types
- Block downloading MSEXE files via HTTP
Task 1 - Create Malware & File Policy
- From the FMC2 UI navigate to Policies -> Malware & File
Click the New File Policy button.
Name your policy Block Malware and click Save - Click + Add Rule to add a new rule.
Change the action to Block Malware
Enable all the options:- Spero Analysis for MSEXE
- Dynamic Analysis
- Capacity Handling
- Local Malware Analysis
- Reset Connection
Check the box against File Type Categories which will select all the File Type Categories, then click All types in selected Categories in the File Types list and click the Add button.
Note: we could have selected all the File Types and added them that way however, if a file type is added in a later release it would not be selected. By selecting all the File Type Categories any new future file types will also be included.
You rule should look like the figure below.
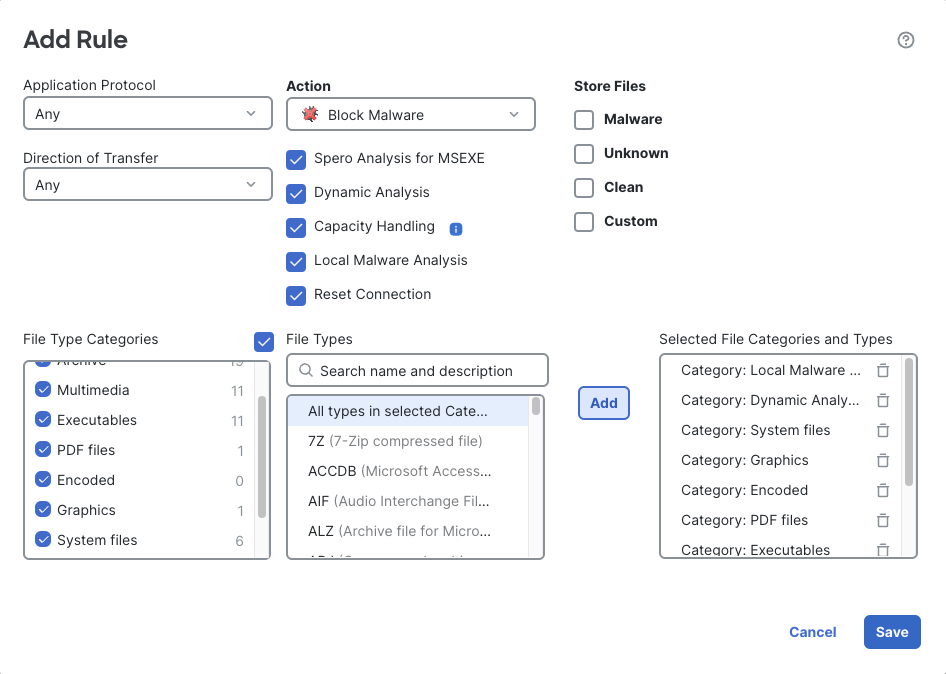
All File Types Rule
Click Save to save the rule.
Note the File Rule notification window.
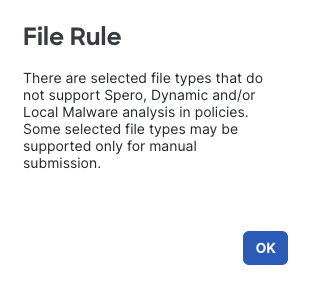
File Rule Notification
This is letting you know that the Dynamic Analysis and Local Malware Analysis options only work on specific file types, because your rule matches all file types those actions may not apply to all files.
-
Now we will create a rule to block download of executable files via HTTP.
Click + Add Rule again to add a new rule.
Under Application Protocol select HTTP
For Direction of Transfer pick Download
For Action pick Block FilesCheck Reset Connection
Under File Type Categories check Executables
Under File Types select MSEXE and click the Add buttonYour rule should look like the figure below.
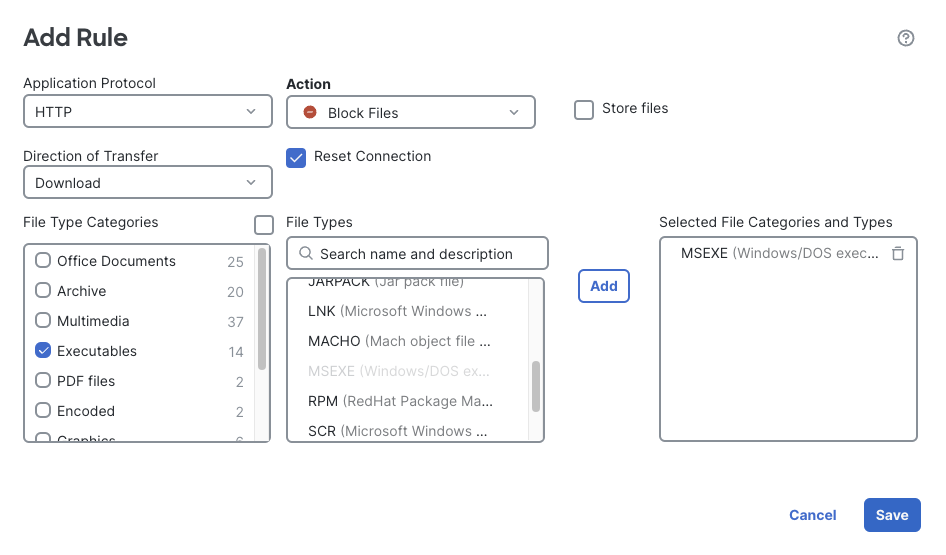
Block MSEXE Rule
ClicK Save to save the rule.
- Notice we have some warning icons by our rules.
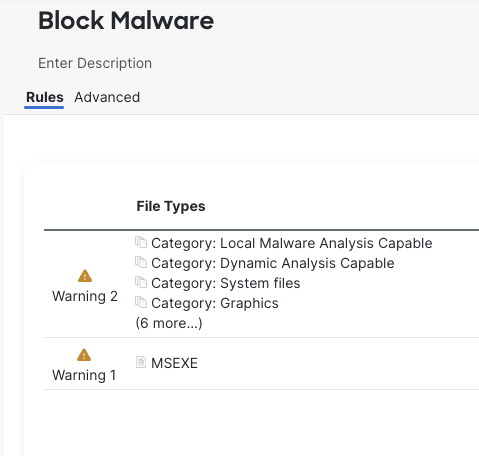
Rule Warnings
Hovering over the warning icons displays a reason message.
Warning 1 indicates the reason is: This rule will block malware lookups on MSEXE files for the rule marked with 'Warning 2'.
Warning 2 indicates: Malware lookups won't occur on MSEXE files because the rule marked with 'Warning 1' will block these files.
This is because while Malware & File rules are unordered, a block rule takes precedence over a rule to alert or inspect files. In this case, the warning is true if the file is transferred via HTTP. However, the first rule will match any supported protocol so the statement is only partially true - MSEXE files transferred via other protocols will still be inspected. As long as we understand the behavior there's no reason to take action on this warning.
Click Save to save the policy
Tell us how we are doing
We are doing our best to ensure the scenarios in this lab guides are useful, clear and work as expected.
Please share your thoughts to help us improve or fix any problems you may run into..
Click here to provide your feedback or report an issue with this guide
Updated over 1 year ago