Scenario 2 - Objects
Before we can setup policies we need to create a few objects. Creating important objects early will make for smoother policy and rule creation later. If we know we will need to use various networks, hosts, ports or other objects in our policies, we can create them now and save having to navigate back and forth later creating objects and then using them in policies or configurations.
You may want to create objects for:
- Internal network ranges
- Snort variable sets
- Network gateways
- Infrastructure hosts such as log, email or DNS servers
Lab Tasks
These are the tasks in this scenario. If you are familiar with the Secure Firewall you may do these on your own, or for step-by-step instructions see below.
- Task 1 - Add the following network objects to FMC2
- Lab-Networks: 198.18.0.0/15
- Corp-LAN: 198.19.10.0/24
- Branch-LAN: 198.19.11.0/24
- Splunk-Server: 198.19.10.15
- Internet-Gateway: 198.18.128.1
- Task 2 - Create a new Variable Set named dCloud-Snort-Variables and add IPv4-Private-All-RFC1918 and Lab-Networks to HOME_NET
Task 1 - Add Objects
-
From the FMC UI, navigate to Objects > Object Management.
- There are a plethora of object types that can be created. When you first arrive at this page you see the Network Objects. There are a number of default host and network objects covering ranges like RFC-1918, multicast or IPv6 link local addresses. For many organizations, the existing RFC-1918 ranges can be used to define local or internal networks. In our case, we also need to add additional dCloud network ranges.
-
Click Add Network at the top of the page and select Add Object.
-
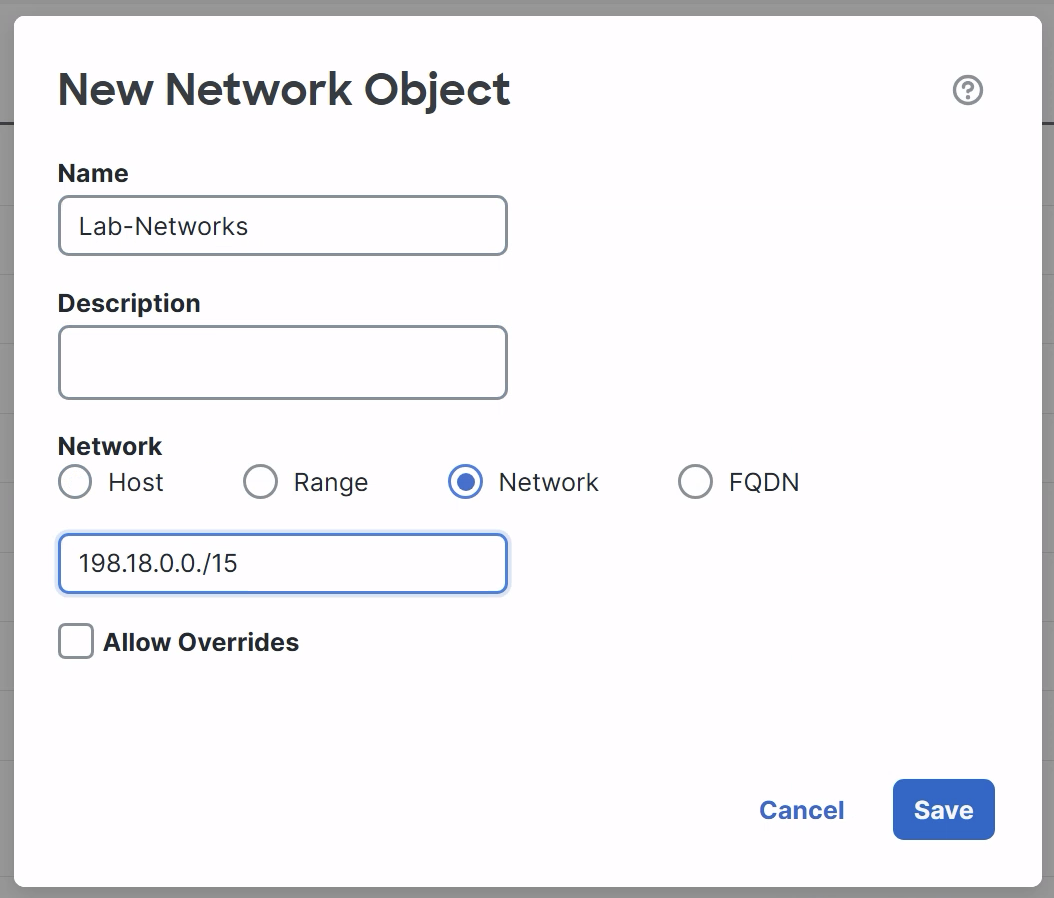
Name the object Lab-Networks.
-
Check the Network radio button.
-
Enter 198.18.0.0/15 for the network range.
-
Click Save.
-
-
Repeat the steps above in Step 2 to create additional Network objects for:
- Corp-LAN 198.19.10.0/24
- Branch-LAN 198.19.11.0/24
-
Create Host objects for:
- Splunk-Server 198.19.10.15
- Internet-Gateway 198.18.128.1
-
You should now have the following objects:
- Lab-Networks: 198.18.0.0/15
- Corp-LAN: 198.19.10.0/24
- Branch-LAN: 198.19.11.0/24
- Splunk-Server (host): 198.19.10.15
- Internet-Gateway (host): 198.18.128.1
Task 2 - Create Variable Set
-
In the left panel, click on Variable Set
Variable Sets are used with Intrusion policy. Variables are used within Snort rules to improve efficiency and reduce false positives. The most important variable to configure is HOME_NET, this could also be considered the protected network. This variable defaults to "any" meaning all networks. However, to improve the efficiency of the system we will define HOME_NET as just our own internal hosts.
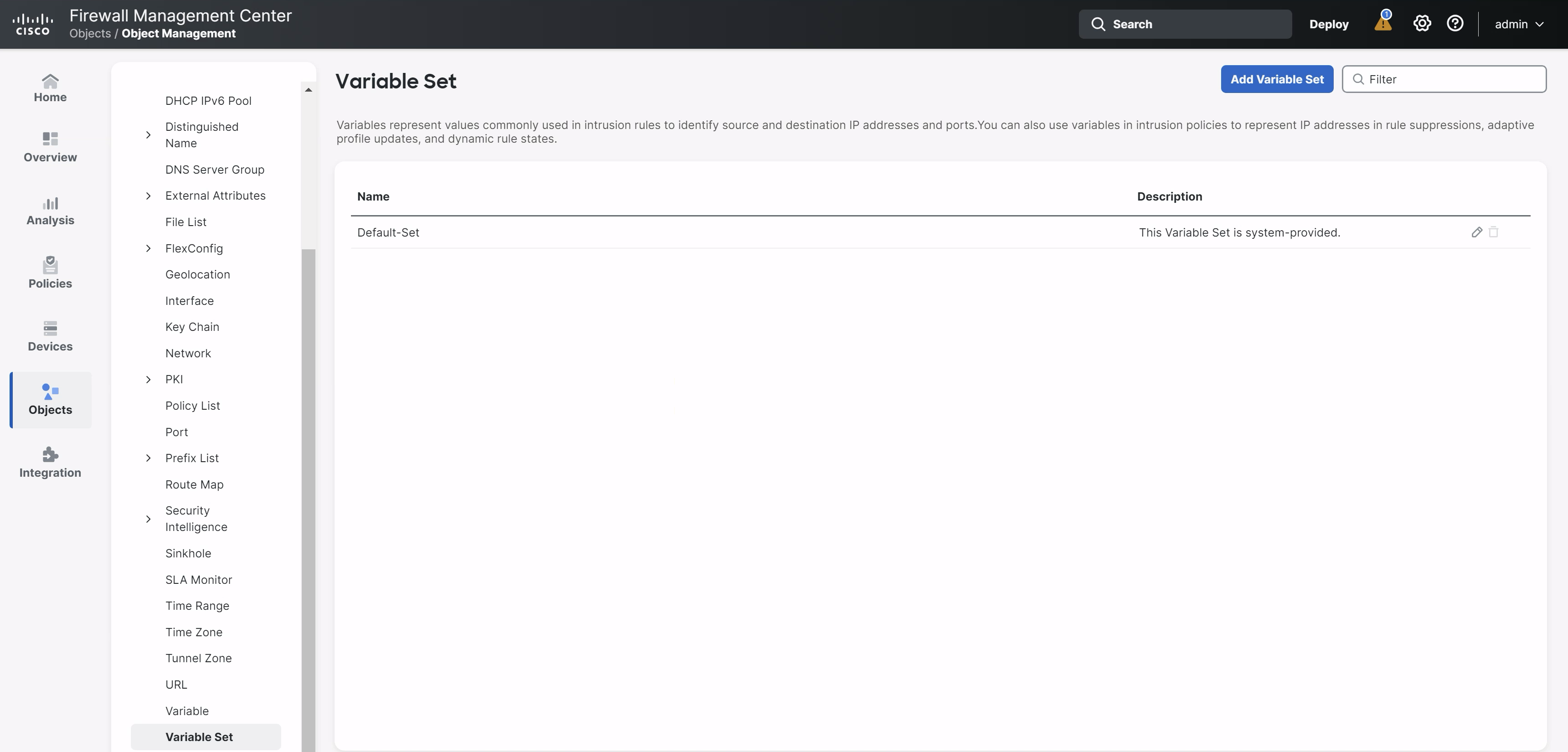
The system ships with a Default-Set. Many organizations can use this single object across all of their Intrusion policies. Larger organizations may want to create additional Variable Sets for devices deployed across multiple network topologies. We will create a dCloud specific Variable Set and use that with our Intrusion policy.
-
Click Add Variable Set.
-
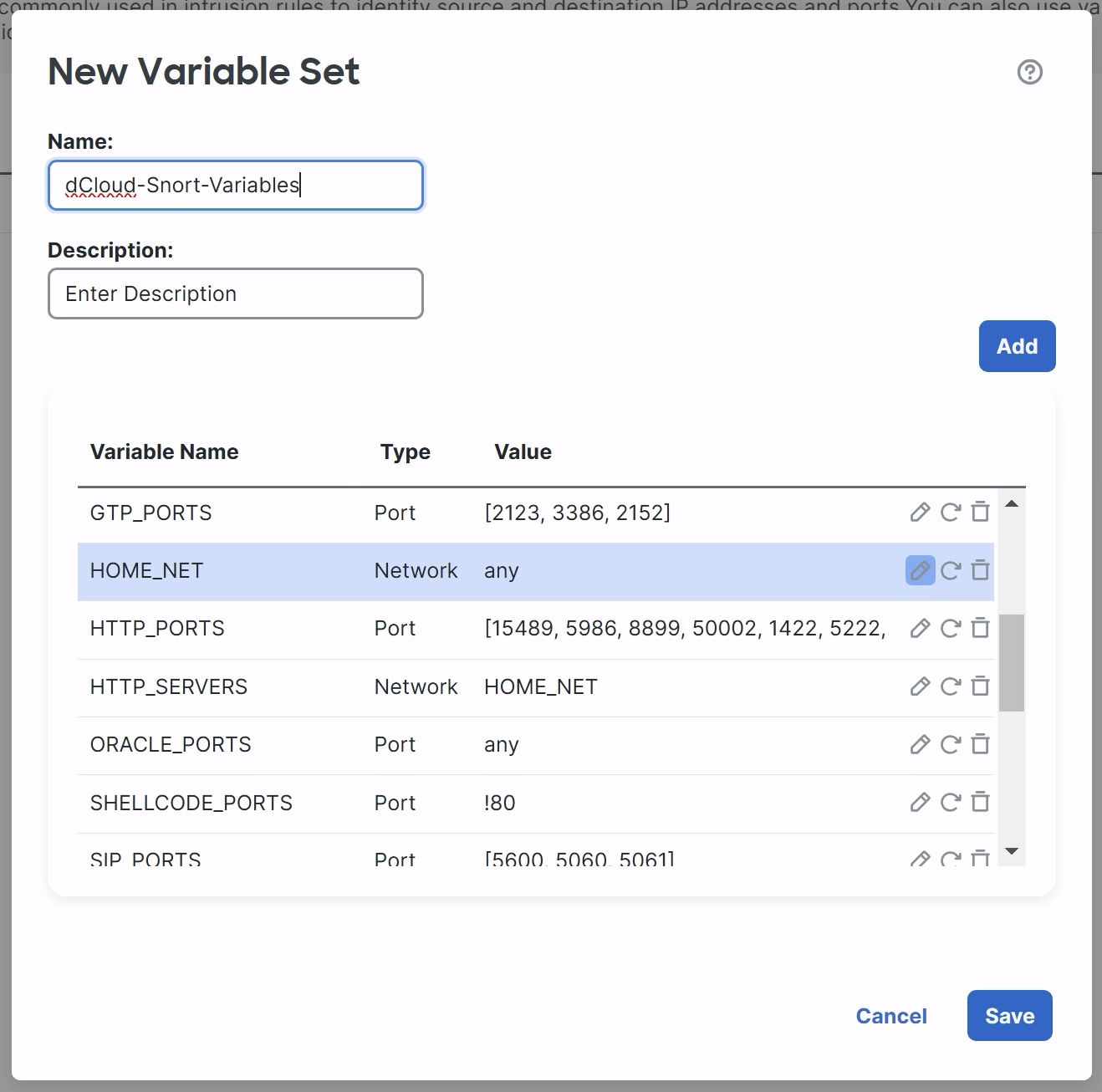
Name your Variable Set dCloud-Snort-Variables
-
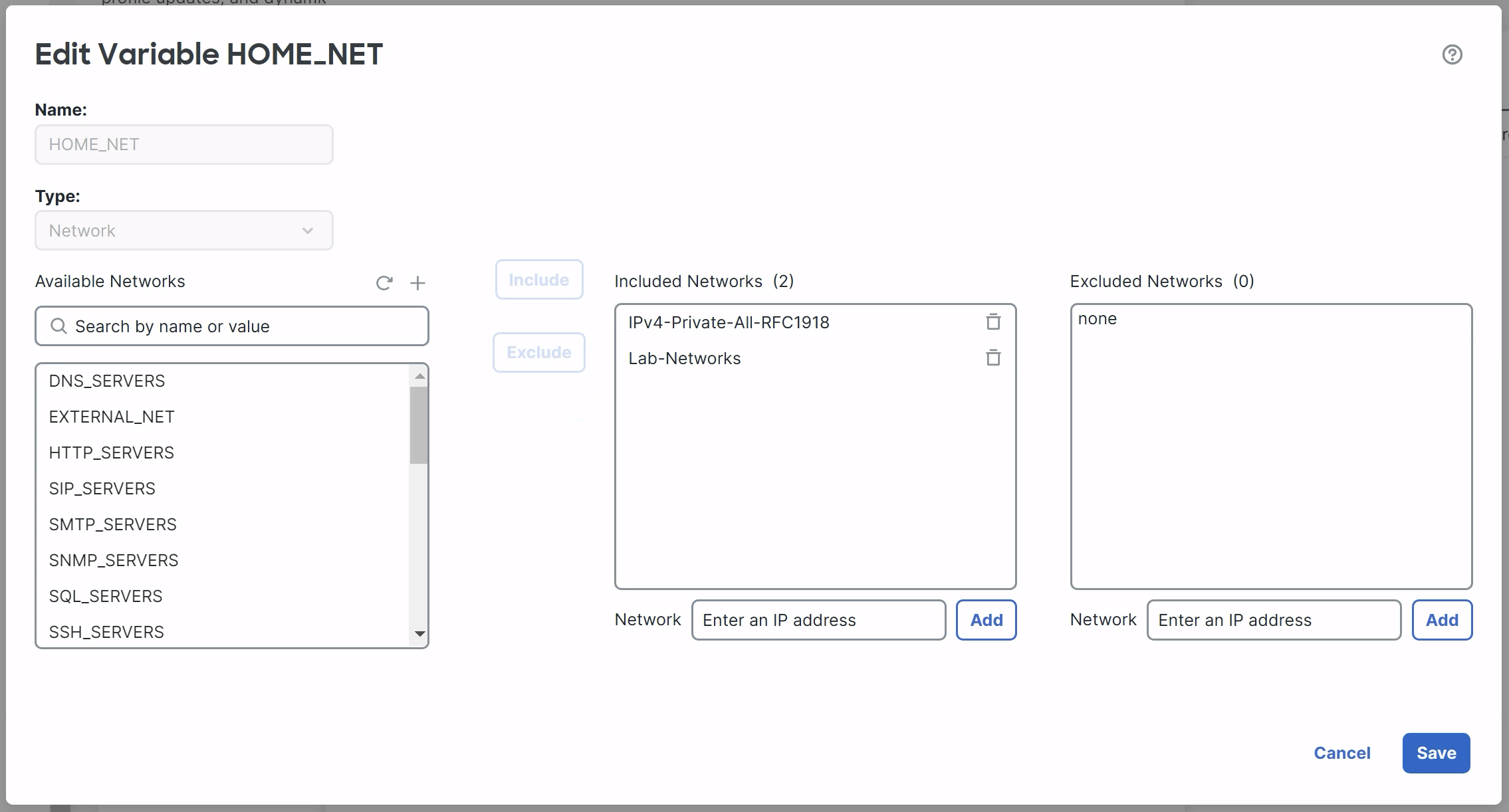
Scroll down and locate the HOME_NET variable, click the pencil icon.
-
We will add the dCloud lab networks and the system object group for all the RFC-1918 addresses to the HOME_NET. Adding all internal IP addresses to HOME_NET is a Secure Firewall best practice.
-
From Available Networks on the left, select IPv4-Private-All-RFC1918 and Lab-Networks and add them to the Included Networks.
-
Click Save to save the HOME_NET changes
-
-
Notice that after customizing HOME_NET it now appears in the list under Customized Variables.
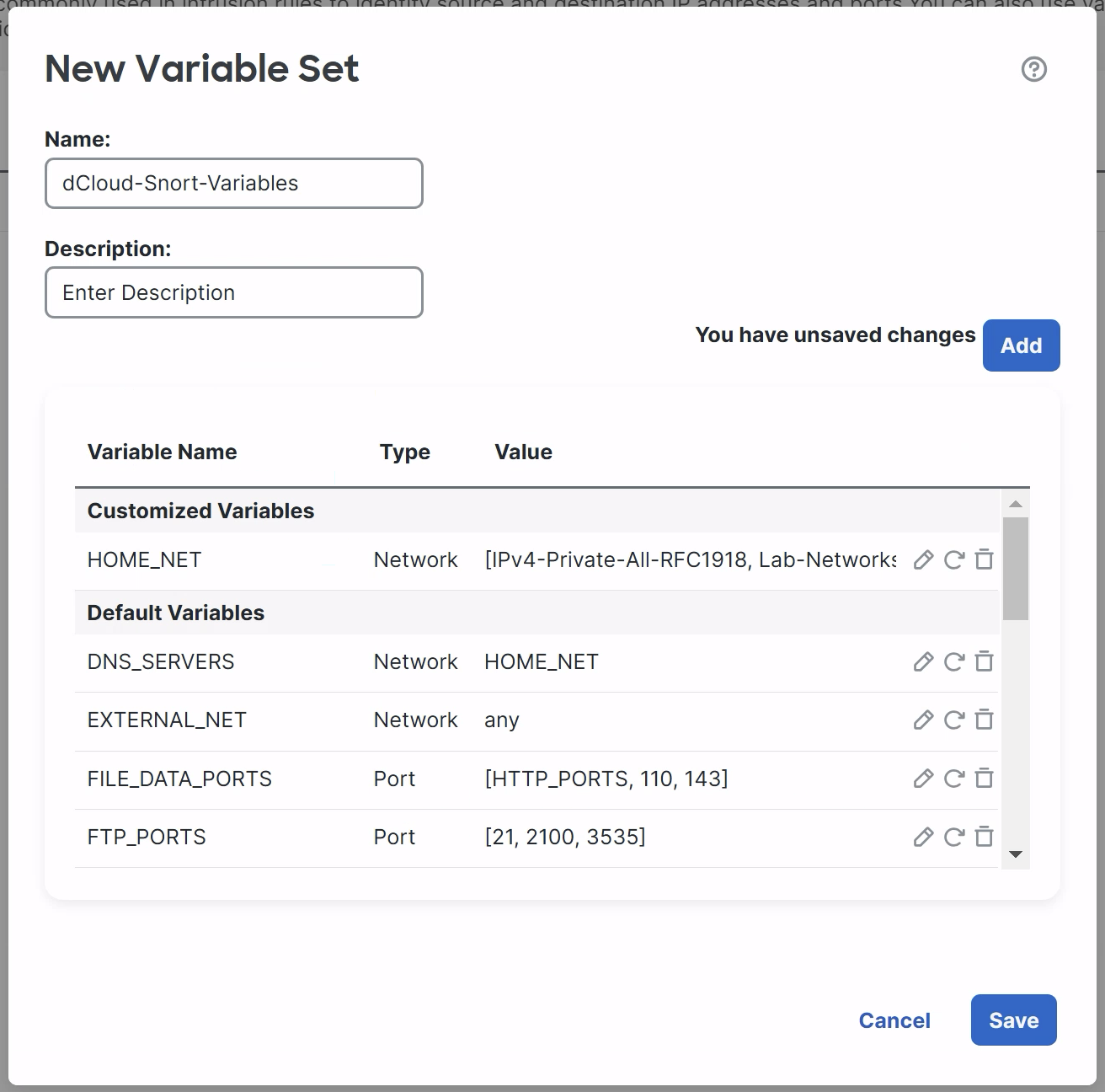
- Customized Variables are specific to this Variable Set. Default Variables are inherited from the Default-Set.
- Click Save to save your new Variable Set.
Tell us how we are doing
We are doing our best to ensure the scenarios in this lab guides are useful, clear and work as expected.
Please share your thoughts to help us improve or fix any problems you may run into..
Click here to provide your feedback or report an issue with this guide
Updated over 1 year ago